Email authentication SPF DKIM DMARC is the difference between "mail delivered" and "why did our invoice vanish?" If your domain can’t prove identity, mailbox providers treat you like a faker. That’s not theory. It’s daily operations now.
Most teams don’t fail because they skipped all three. They fail because they set them up in the wrong order, publish a harsh policy too early, and block their own mail. If you’re still sorting out basic business email decisions, fix that first. Then come back and lock down authentication the right way.
This guide gives you the safe rollout for email authentication SPF DKIM DMARC: SPF first, DKIM second, DMARC last. That order matters. Get it wrong and forwarded mail breaks, marketing tools fail alignment, and support mail starts disappearing.
If you’re using TrekMail, the platform already checks your DNS health and supports custom domains, IMAP mailboxes, catch-all routing, mailbox forwarding, migration, and either BYO SMTP or managed SMTP. If you’re still adding a domain, start with TrekMail’s domain setup guide. If you’re building from scratch, this article on how to create email with a domain fills in the basics.
What email authentication SPF DKIM DMARC actually does
Email authentication SPF DKIM DMARC is a three-part trust system. SPF says which servers may send, DKIM proves the message wasn’t altered, and DMARC tells receivers what to do when those checks fail or don’t align with your visible From domain.
| Protocol | Job | Checks | Main failure mode |
|---|---|---|---|
| SPF | Authorization | Whether the sending server is allowed | Too many lookups, missing sender, forwarding breaks it |
| DKIM | Integrity | Whether headers and body still match the signature | Bad selector, missing key, vendor not signing with your domain |
| DMARC | Policy and alignment | Whether SPF or DKIM aligns with the From domain | Turning on enforcement before SPF and DKIM are clean |
Think of SPF as the guest list, DKIM as the tamper seal, and DMARC as the rulebook. You need all three, but not all at once. Email authentication SPF DKIM DMARC works best when you stage it instead of dumping records into DNS and hoping for the best.
The safest setup order
The correct setup order for email authentication SPF DKIM DMARC is simple: inventory senders, publish SPF, enable DKIM everywhere, monitor DMARC, then enforce DMARC. That sequence avoids the classic mistake of rejecting legitimate mail before you know what is actually sending from your domain.
- Inventory every system that sends mail as your domain.
- Publish one SPF record with all legitimate senders.
- Enable DKIM for each sender or vendor.
- Publish DMARC with
p=noneand collect reports. - Fix alignment failures.
- Move to
p=quarantine, thenp=reject.
That’s the whole playbook. Email authentication SPF DKIM DMARC is not hard because the records are long. It’s hard because your sending stack is usually messier than you think.
Phase 1: Inventory and SPF
SPF should be your first live change because it answers a basic question: who is allowed to send for this domain? It won’t fix everything, but it gives you a clean starting point and exposes old vendors you forgot were still authorized.
Before touching DNS, list every sender. Corporate mail. Billing tools. CRM. Help desk. Marketing platform. Website forms. Printers. Anything that sends as @yourdomain.com belongs on the sheet.
Then publish one SPF record. One. Not two. Not "one for Google and one for marketing." Multiple SPF TXT records cause a fail state. TrekMail’s docs call that out directly in their DNS setup examples.
Type: TXT
Host: @
Value: v=spf1 include:spf.trekmail.net include:amazonses.com ~allUse ~all while you’re still validating traffic. Save -all for later if you’re certain the record is complete.
The big SPF trap is the lookup limit. Per RFC 7208, SPF evaluation has a hard limit of 10 DNS-mechanism lookups. Pile up enough include:, a, or mx mechanisms and the record can fail with permerror. That means your beautifully documented SPF record becomes useless in production.
You add Google, HubSpot, Zendesk, QuickBooks, Mailchimp, and one old ticketing system nobody remembers. SPF looks "complete." Then a receiver hits the lookup cap and treats the whole thing as broken.
If you run a lot of domains, email authentication SPF DKIM DMARC gets operational fast. Audit vendors aggressively. Remove dead includes. Split traffic by subdomain when needed. If you manage many client domains, this matters even more. That’s one reason teams move toward multi domain email hosting with centralized DNS checks.
Phase 2: DKIM and alignment
DKIM comes second because SPF alone is fragile. Forwarding commonly breaks SPF, but DKIM can still pass if the message stays intact. For email authentication SPF DKIM DMARC, DKIM is usually the protocol that saves legitimate mail when it takes a weird route.
Enable DKIM in every service that sends mail for your domain. Every service. Your mailbox provider. Your transactional platform. Your marketing tool. Your help desk. If one of them can’t sign with your domain, treat that as a product problem, not a cute limitation.
Typical DKIM DNS looks like this:
Type: TXT
Host: trek._domainkey
Value: v=DKIM1; k=rsa; p=MIIBIjANBgkqh...Some vendors use CNAME-based DKIM instead of a TXT public key. Fine. The method changes. The requirement does not.
Use separate selectors per vendor when possible. That gives you clean revocation. If one platform is compromised or retired, you remove its selector without breaking your main mailbox flow.
Now the alignment piece. This is where email authentication SPF DKIM DMARC setups quietly fail. Authentication by itself is not enough. DMARC cares whether the authenticated domain lines up with the visible From domain. Google’s sender guidance says either SPF alignment or DKIM alignment must match the organizational domain in the From header, and they recommend full alignment on both where possible. See Google’s sender guidelines FAQ.
If Mailchimp signs with its domain and uses its own return-path, you may see SPF pass and DKIM pass somewhere, but DMARC still fail for your visible From address. The fix is custom domain authentication inside that vendor. No shortcut. No exception.
Forwarding is the classic case. If your team forwards mail a lot, read email forwarding setup and fix. Email authentication SPF DKIM DMARC often breaks there first.
Phase 3: DMARC in monitor mode
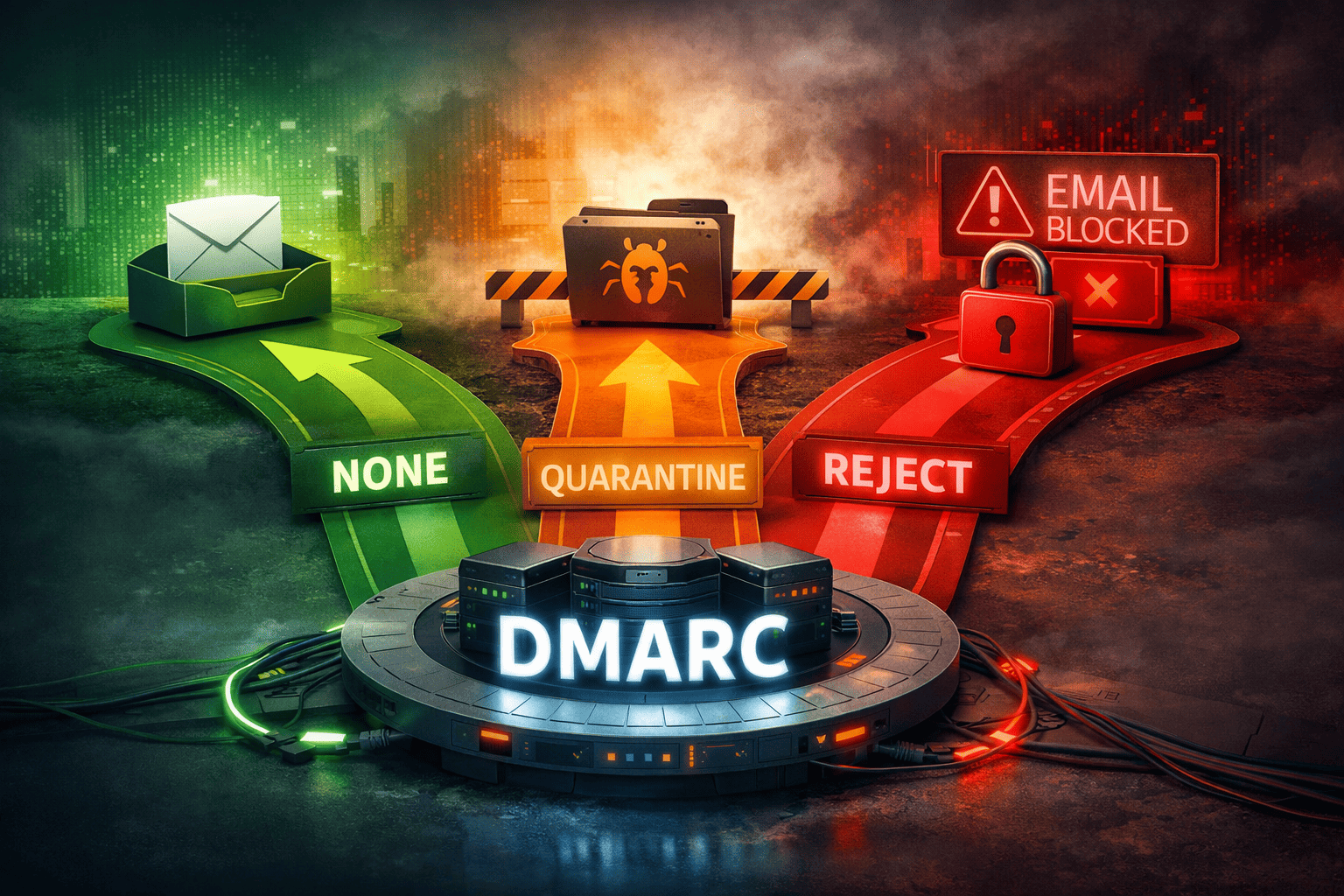
DMARC should start in monitor mode, not enforcement. Publishing p=none lets you see who is sending as your domain before you tell receivers to junk or reject anything. That keeps you from causing your own outage.
Start with a basic record:
Type: TXT
Host: _dmarc
Value: v=DMARC1; p=none; rua=mailto:dmarc@yourdomain.com; adkim=s; aspf=sYou can use relaxed alignment defaults if needed, but strict alignment keeps the rules obvious. Either way, don’t jump straight to reject unless you already know every legitimate sender and every one of them aligns.
DMARC reports are useful, but raw XML is miserable. Use a parser or dashboard. TrekMail’s spam troubleshooting docs explain the key reading: SPF fail plus DKIM pass can still be fine, especially on forwarded mail. Both failing is the real problem. If you’re checking deliverability inside TrekMail, their spam troubleshooting guide is the practical place to start.
This is the stage where email authentication SPF DKIM DMARC stops being theory. You’ll find forgotten systems, broken scanners, old newsletters, and maybe outright spoofing. Good. Better to find them in reports than after a customer misses a contract.
Phase 4: Fix what the reports show
DMARC reports tell you which senders are aligned, which are merely authenticated, and which are fake. Your job is to separate legitimate failures from spoofing and then clean up the legitimate ones until email authentication SPF DKIM DMARC is passing consistently for real traffic.
Most failures land in a few buckets:
- A real sender is missing from SPF.
- A vendor signs DKIM, but not with your domain.
- A marketing platform uses a default bounce domain, so SPF alignment fails.
- A device is sending direct mail instead of relaying through authenticated SMTP.
- An attacker is spoofing your From domain from random IPs.
Printers and scanners are repeat offenders. Stop letting them spray mail directly onto the internet. Route them through a real SMTP relay. On TrekMail paid plans, managed SMTP is included; on Nano, you bring your own SMTP. If you need client settings, TrekMail’s IMAP and SMTP settings guide documents the current hosts and ports. TrekMail is IMAP only, not POP3.
Once email authentication SPF DKIM DMARC is clean in reports for a couple of weeks, move up carefully.
v=DMARC1; p=quarantine; rua=mailto:dmarc@yourdomain.com
v=DMARC1; p=reject; rua=mailto:dmarc@yourdomain.comGo to quarantine first if you want a softer landing. Go to reject once you trust your inventory and alignment.
How to verify the records from the command line
Verification matters because DNS panels lie, caches linger, and vendor dashboards can lag. The fastest way to confirm email authentication SPF DKIM DMARC is to query DNS directly and then send live test messages through every system that uses your domain.
Check SPF:
dig txt example.com +shortCheck DKIM for a selector:
dig txt trek._domainkey.example.com +shortCheck DMARC:
dig txt _dmarc.example.com +shortLook for one SPF record, a valid DKIM public key, and the DMARC policy you intended to publish. If you changed a record and nothing is showing, wait for TTL and query an external resolver.
Also check the boring infrastructure. Reverse DNS still matters. TLS still matters. Complaint rates still matter. Email authentication SPF DKIM DMARC is foundational, not magical. It gets you in the game. It does not excuse bad lists or reckless sending.
The old way vs the new way
The old way was paying per mailbox just to inherit someone else’s defaults. The new way is controlling your own domain, your own SMTP path, and your own authentication without paying a seat tax for apps you didn’t ask for.
That matters if you manage multiple brands, clients, or shared inboxes. TrekMail starts at $3.50 per month on Starter, offers a Nano plan at $0 with BYO SMTP, and includes managed SMTP on paid plans. You get custom domains, IMAP mailboxes, catch-all, mailbox forwarding, server-side IMAP migration, and API access on higher tiers. If you’re comparing options, the difference is simple: the old stack charges per user; the new stack charges for the platform.
That’s the operator angle. Set up email authentication SPF DKIM DMARC once, keep it healthy, and stop paying extra every time you create another mailbox. If you want the flat-rate model explained from the business side, read set up email on my domain, then review plans at TrekMail pricing.
Conclusion
Email authentication SPF DKIM DMARC only feels confusing when people treat it like three unrelated DNS chores. It’s one system. SPF authorizes. DKIM signs. DMARC enforces alignment and policy. Follow that order and you avoid the self-inflicted outages that wreck deliverability.
If you want the shortest version, here it is: inventory senders, publish one SPF record, enable DKIM everywhere, monitor DMARC, fix alignment, then enforce. That’s the cleanest path to reliable email authentication SPF DKIM DMARC in 2025 and 2026. If you want to do it without per-user pricing, start at TrekMail.