A DMARC reject policy is the point where monitoring ends and enforcement starts. At p=none, you get reports but spoofed mail can still land. If you jump to p=reject too early, your own invoices, password resets, and support replies can get blocked. If you need the basics first, start with business email and come back when your domain is sending cleanly.
That’s the problem. The pain is simple: attackers don’t wait while you sit in monitoring mode, and receivers won’t forgive sloppy authentication once you publish a strict DMARC reject policy. This guide gives you a go or no-go checklist, the rollout sequence, and the failure patterns that matter in 2025 and 2026.
| Prerequisite | Target | Why it matters before a DMARC reject policy |
|---|---|---|
| Volume soak | 30 days minimum | Catches monthly and irregular mail streams before enforcement blocks them |
| Alignment audit | 100% of legitimate senders aligned | SPF or DKIM pass alone is not enough for DMARC |
| Reputation check | Spam rate under 0.1% | Bad reputation plus strict policy is a bad mix |
| Forwarding survival | DKIM survives forwarding | SPF usually breaks when mail is relayed |
| Subdomain policy | sp tag reviewed | Root policy can accidentally break dev or legacy subdomains |
What a DMARC reject policy actually does
A DMARC reject policy tells receiving servers to reject mail that fails DMARC evaluation for your domain. In plain English: if neither aligned SPF nor aligned DKIM passes, the receiver should refuse the message instead of delivering it or dropping it into spam. That is real protection, not just visibility.
The important word there is aligned. People remember SPF and DKIM. They forget that DMARC cares whether one of them matches the domain in the visible From header. That gap is where most self-inflicted outages happen.
Per RFC 7489, receivers can sample policy with pct and can apply local judgment on final disposition. So a DMARC reject policy is powerful, but it is not magic. It will not fix bad reputation, bad content, or a broken sending setup.
Prerequisite 1: Run a 30-day soak before a DMARC reject policy
A DMARC reject policy should never be based on one clean week of reports. Thirty days is the practical minimum because business email is lumpy. Monthly billing runs, quarterly reports, welcome emails, and low-volume support automations often hide outside a short test window.
This is where teams get burned. They check seven days of DMARC aggregate reports, see nothing scary, publish p=reject, and then the next invoice run starts bouncing.
Example: your SaaS billing tool sends only on the first of the month. It authenticates fine on its own domain, but its DKIM is still signing as the vendor and its bounce domain is unaligned. At
p=none, you barely notice. Atp=reject, customers stop getting invoices.
Spend the soak period looking for senders that appear once or twice but carry high-value traffic. Billing systems, HR systems, scanner alerts, form plugins, and support desks are the usual culprits. A DMARC reject policy should be the last step in discovery, not the first.
If your DNS setup is still shaky, fix that before you interpret the reports. TrekMail’s required DNS records guide shows the baseline records TrekMail expects, including SPF, DKIM, MX, and DMARC.
Prerequisite 2: Audit alignment, not just authentication
A DMARC reject policy only works safely when every legitimate sender has aligned SPF or aligned DKIM. Plenty of tools pass authentication while still failing DMARC because the authenticated domain does not match the visible From domain.
This is the classic SaaS trap.
Header From:
support@yourcompany.com
Return-Path:bounce.vendor-mail.comand SPF passes there
DKIM:d=vendor-mail.comand DKIM passes there
Result: DMARC fails foryourcompany.com
That setup looks healthy inside the vendor dashboard. It is not healthy for your domain. Under a DMARC reject policy, those messages can get blocked.
The fix is vendor-side domain authentication. That usually means:
- Publishing the vendor’s DKIM records so it can sign with your domain.
- Configuring a custom bounce or return-path domain for SPF alignment.
- Testing real messages and reading the headers, not just trusting a green checkbox.
Watch your SPF record while you do this. You only get ten DNS lookups before SPF falls over. TrekMail’s domain setup guide calls out the common mistake of creating multiple SPF TXT records instead of one merged record.
Prerequisite 3: Check reputation before a DMARC reject policy
A DMARC reject policy blocks spoofing, but it does not clean up a dirty sender reputation. If your spam complaint rate is already high, strict DMARC can make the signal louder: you are telling receivers that this mail really is yours.
Google’s sender guidance is blunt. Bulk senders should keep spam rates below 0.1% and avoid ever reaching 0.3% or higher, which Google says can affect mitigation eligibility. Yahoo’s sender best practices also call out 0.3% as the ceiling to stay under.
Read that as an operator, not a marketer. If Postmaster shows 0.18%, you do not have a DMARC problem. You have a list quality or mail relevance problem. Fix that first. Then move policy.
Check these before publishing a DMARC reject policy:
- Google Postmaster Tools spam rate for your primary sending domain.
- Complaint spikes tied to one campaign, one list, or one tool.
- Bounce patterns that suggest old data or role accounts.
- Whether transactional and marketing mail share the same domain reputation.
Authority sources: Google sender guidelines FAQ and Yahoo sender best practices.
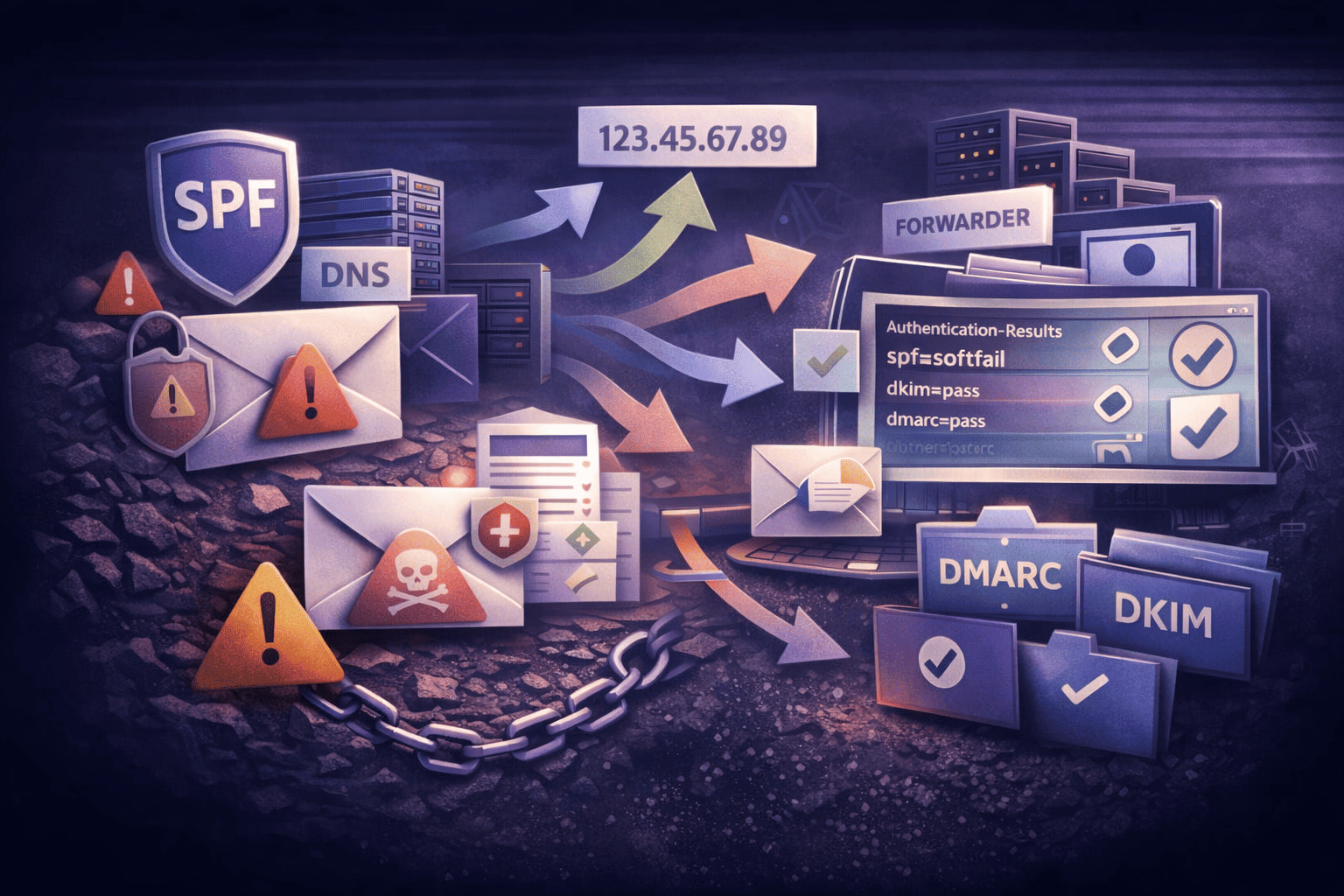
Prerequisite 4: Make forwarding survive your DMARC reject policy
A DMARC reject policy is safe with forwarding only when DKIM survives the trip. SPF often fails after forwarding because the forwarder’s server is not in your SPF record. That is normal. DKIM is what keeps legitimate forwarded mail alive.
This point gets missed because SPF failures look scary in aggregate reports. They are not always scary. Forwarders, mailing lists, and security gateways regularly break SPF. If DKIM is intact and aligned, DMARC still passes.
That’s why forwarding readiness is really DKIM readiness. If you depend on forwarding workflows, get aggressive about DKIM on every important stream before you publish a DMARC reject policy.
TrekMail’s spam troubleshooting doc spells this out clearly: SPF fail plus DKIM pass is common when mail is forwarded, and TrekMail recommends managed sending on paid plans so mail is signed with your domain’s DKIM key. If you use forwarding heavily, also read email forwarding so you know where forwarding breaks and where it doesn’t.
If you are hosting on TrekMail, the docs worth checking are My Emails Go to Spam and IMAP & SMTP settings. The first explains why SPF failures can be harmless when DKIM passes. The second confirms TrekMail is IMAP-first and how outbound SMTP works by plan.
Prerequisite 5: Set a subdomain policy before a DMARC reject policy at the root
A DMARC reject policy on the root domain can also affect subdomains. If you have mail coming from dev.example.com, alerts.example.com, or some forgotten tool on a subdomain, root enforcement can break it unless you review the sp tag.
This is where real-world DNS gets messy. Production may be clean while staging, printers, scanners, or abandoned tools on subdomains are a mess. DMARC inheritance means the mess stops being invisible.
Use the sp tag to control that blast radius:
v=DMARC1; p=reject; sp=none; rua=mailto:dmarc@example.comThat record says: enforce strictly on the main domain, but leave subdomains in monitoring mode for now. Later, once you have audited them, you can tighten the subdomain policy too.
This is also where a DMARC reject policy becomes unexpectedly useful. The first weeks of reject-mode reporting often expose shadow IT: old CRMs, forgotten marketing tools, orphaned app servers, or one developer’s relay from two years ago. DMARC is not just anti-spoofing. It is an audit of what your company is actually sending.
Roll out a DMARC reject policy in stages, not all at once
A DMARC reject policy should be the end of a staged rollout. Use quarantine first, then sample policy with pct, then move to full reject only after you have seen stable reports and no legitimate traffic going missing.
The practical path looks like this:
- Start with 10% quarantine for one week.
- Move to 100% quarantine for another one to two weeks.
- Publish full reject only after support, billing, auth, and forwarding look clean.
v=DMARC1; p=quarantine; pct=10; rua=mailto:dmarc@example.comv=DMARC1; p=quarantine; rua=mailto:dmarc@example.comv=DMARC1; p=reject; rua=mailto:dmarc@example.comThere is a reason to do this even if you think your setup is perfect. Quarantine gives users a recoverable failure mode. Reject does not. Once a strict DMARC reject policy is live, a legit message can die before anybody sees it.
Old way vs new way: managing a DMARC reject policy across many domains
A DMARC reject policy is manageable on one domain. It gets ugly fast when you run ten, fifty, or five hundred. Every vendor has its own DKIM steps. Every domain has its own DNS drift. Every client swears they only send from one tool until DMARC reports say otherwise.
Old way: parse XML reports by hand, chase vendor IPs, patch records one domain at a time, and hope nobody added another sender in the background.
New way: centralize the domains, standardize DNS, and use a mail platform that does not make authentication harder than it needs to be.
That is where TrekMail fits. Paid plans start at $3.50 per month, include managed SMTP, and give you one place to manage domains, IMAP mailboxes, forwarding, and DNS health. The Nano plan stays free for up to 10 domains with BYO SMTP. If you are running lots of brands or client domains, TrekMail is built for multi domain email hosting, not one-domain-at-a-time babysitting.
For solo founders and small teams, the value is simpler: fewer moving parts in your main mail flow. For agencies and MSPs, the value is margin. One standardized setup. Less time chasing broken SPF includes. Fewer panicked tickets after a client asks for a strict DMARC reject policy.
If you want the product details, use TrekMail’s docs for required DNS records and pricing at trekmail.net/pricing. There’s a 14-day free trial for paid plans, credit card required, and the Nano plan does not need a card at all.
Conclusion: when to publish a DMARC reject policy
A DMARC reject policy is the right move when five things are true: you have at least 30 days of clean reporting, every legit sender is aligned, complaint rates are under control, forwarding survives on DKIM, and your subdomain policy is intentional. Miss one of those and you are still in prep mode.
Do the boring work first. Audit the senders. Read the headers. Fix the DNS. Then publish the DMARC reject policy and stop letting attackers spoof your domain for free.
If you want less DNS wrestling and a cleaner path to enforcement, start at TrekMail or compare plans at trekmail.net/pricing.