DMARC fail tickets usually show up after you think the hard part is over. SPF is live. DKIM is live. Your DMARC policy is finally on p=quarantine or p=reject. Then a real message gets forwarded and disappears. It wasn’t spoofed. It wasn’t spam. It just took a path your setup couldn’t survive.
That’s the real problem with dmarc fail during forwarding. The message is legitimate, but the forwarding hop changes enough of the delivery context that receivers stop trusting it. If you only understand SPF and DKIM at the checkbox level, this looks random. It isn’t. There’s a pattern, and once you see it, you can fix it.
If you need the wider setup baseline first, start with business email. If forwarding is already in your stack, this pairs well with email forwarding.
What a DMARC fail actually means
A dmarc fail means the message did not produce an aligned SPF pass or an aligned DKIM pass for the visible From domain. Passing authentication alone is not enough. DMARC cares whether the authenticated domain matches the domain the recipient sees.
DMARC sits on top of SPF and DKIM. Per RFC 7489, a message passes DMARC if at least one of these is true:
- SPF passes and aligns with the Header From domain.
- DKIM passes and aligns with the Header From domain.
That sounds simple. In practice, dmarc fail happens because operators confuse three separate ideas:
- Authentication: Did SPF or DKIM pass?
- Alignment: Did the passing domain match the Header From domain?
- Forwarding survival: Did the message stay intact across the hop?
You can pass SPF and still get a dmarc fail. You can pass DKIM and still get a dmarc fail. If the passing identity belongs to the wrong domain, DMARC treats it like a miss.
Why forwarding causes DMARC fail so often
Forwarding causes dmarc fail because the forwarder changes the path and sometimes the content. SPF depends on path. DKIM depends on message integrity. A forwarded message often breaks one, and badly configured systems break both.
Here’s the common path:
- A sender transmits mail from
sender.com. - An intermediate mailbox or gateway receives it.
- That system auto-forwards the message to Gmail, Outlook, or another destination.
At that point, the receiver no longer sees the original sender IP as the SMTP client. It sees the forwarder’s IP.
That is where dmarc fail starts.
SPF breaks first
SPF is defined in RFC 7208. It checks whether the connecting IP is allowed to send for the envelope domain.
Once a message is forwarded, the connecting IP is the forwarder, not the original sender. So SPF almost always fails on forwarded mail unless the forwarder rewrites the envelope sender with SRS.
Original path:
sender.comsends from IP A. SPF passes.
Forwarded path: intermediary forwards from IP B. Receiver checkssender.comagainst IP B. SPF fails.
This SPF failure alone does not guarantee dmarc fail. If aligned DKIM survives, DMARC still passes. That’s why good DKIM matters more than most teams think.
DKIM is supposed to save the message
DKIM, defined in RFC 6376, signs selected headers and the body. It does not care which IP forwards the message. That makes DKIM the normal rescue path when SPF dies.
But DKIM only helps if two things are true:
- The signature is still valid after forwarding.
- The
d=domain aligns with the visible From domain.
If either piece is wrong, you get another dmarc fail.
Forwarders often modify mail in small but destructive ways:
- Adding
[EXTERNAL]to the subject - Appending disclaimers or legal footers
- Rewriting MIME boundaries
- Changing line wrapping or whitespace
Some changes survive relaxed DKIM canonicalization. Some do not. Aggressive gateways break signatures every day. That’s why a dmarc fail on forwarded mail is usually not a spoofing event. It’s an implementation event.
The alignment trap that triggers DMARC fail without forwarding
A dmarc fail does not require forwarding. It also happens when your SaaS sender authenticates with its own domain instead of yours. The mail is real, but the alignment is wrong, so DMARC still fails.
This one catches operators constantly.
Example:
- From:
billing@yourcompany.com - Return-Path:
bounce.vendor-mail.com - DKIM:
d=vendor-mail.com
SPF may pass for vendor-mail.com. DKIM may pass for vendor-mail.com. But DMARC still shows dmarc fail because neither authenticated identity aligns with yourcompany.com.
The fix is custom domain authentication. Your ESP has to sign with your domain, not theirs.
If you’re moving off alias-heavy setups, read domain email alias vs mailbox. A lot of “random” authentication issues start there.
How to diagnose a DMARC fail from headers
You can diagnose most dmarc fail cases in a minute if you read the headers instead of guessing. Start with Authentication-Results, then compare SPF, DKIM, and alignment domains.
Ask the recipient for full headers. Then look for something like this:
Authentication-Results: mx.google.com;
spf=fail smtp.mailfrom=sender.com;
dkim=pass header.i=@sender.com header.s=mail;
dmarc=pass header.from=sender.comThat means forwarding probably broke SPF, but DKIM survived. No real problem.
This is the dangerous version:
Authentication-Results: mx.google.com;
spf=fail smtp.mailfrom=sender.com;
dkim=fail header.i=@sender.com;
dmarc=fail header.from=sender.comThat is the classic forwarding dmarc fail. SPF died because the path changed. DKIM died because the message changed or the signature was already weak.
| Header result | What it usually means | What to do |
|---|---|---|
spf=fail, dkim=pass, dmarc=pass | Normal forwarding behavior | Do nothing. Monitor only. |
spf=fail, dkim=fail, dmarc=fail | Forwarding plus content rewrite or broken DKIM | Fix DKIM signing and canonicalization first. |
dkim=pass but wrong d= domain | Alignment trap with ESP or relay | Enable custom domain DKIM. |
spf=permerror | SPF record too complex or malformed | Reduce includes and flatten or split by subdomain. |
arc=pass | Forwarder preserved trust chain | Usually no action needed. |
How to stop DMARC fail on forwarded mail
You won’t stop people from forwarding mail. You stop dmarc fail by designing for forwarding instead of pretending it won’t happen. That means strong aligned DKIM, sane SPF, and a forwarding path that doesn’t mutilate messages.
1. Treat DKIM as mandatory, not optional
If you care about mail surviving a forward and avoiding dmarc fail on legitimate messages, DKIM is your lifeline. Sign every outbound stream. Not just newsletters. Not just support. Everything.
Your signature needs to align with the visible From domain. If the message says it came from yourdomain.com, the signing domain should be yourdomain.com or an aligned subdomain.
In TrekMail, the DNS side starts with the required records in Required DNS Records. If DNS health is still yellow or red, don’t expect a forwarding edge case to work.
2. Use relaxed DKIM canonicalization
Strict DKIM is brittle. Tiny formatting changes can trigger dmarc fail. Relaxed canonicalization gives legitimate mail a better chance to survive minor whitespace and header normalization.
DKIM-Signature: v=1; a=rsa-sha256; d=example.com; s=mail;
c=relaxed/relaxed; h=from:to:subject:date:message-id; ...This won’t save mail from a forwarder that appends a giant footer to the body, but it helps with normal transit noise.
3. Don’t let vendors sign as themselves
If your CRM, help desk, or newsletter tool signs mail with d=vendor.com, you are one forwarding hop away from another dmarc fail ticket. Fix the vendor config now. Custom return-path and custom DKIM are not optional if you send as your own brand — otherwise the next dmarc fail is just a forwarding hop away.
4. Keep SPF short enough to work
SPF doesn’t just fail on forwarding. It also fails when your record turns into a junk drawer. RFC 7208 caps SPF evaluation at 10 DNS lookups. Hit that limit and you can get permerror, which removes SPF as a usable DMARC path.
dig +short TXT example.com
dig +short TXT _dmarc.example.comIf you’ve piled Google, Microsoft, Mailgun, SendGrid, Zendesk, and three old hosts into one SPF record, clean it up. Move tools to subdomains where it makes sense.
5. Understand what SRS and ARC can and can’t do
SRS can prevent SPF from failing at the transport level by rewriting the envelope sender during forwarding. ARC can preserve the authentication verdict from an upstream hop so the final receiver can make a better decision. Neither one excuses sloppy DKIM — a dmarc fail caused by broken signatures won't be saved by transport-layer patches alone.
Google’s current sender guidance says forwarded mail does not need DMARC alignment in the same way direct mail does, but forwarding services should add ARC headers. That matters in 2025 and 2026 because large providers are less tolerant of messy indirect mail than they used to be.
If you run lots of forwarded mailboxes, this is where platform choice matters. TrekMail supports mailbox forwarding and standards-first DNS setup, and its docs for Bring Your Own SMTP make the alignment tradeoffs explicit instead of hiding them.
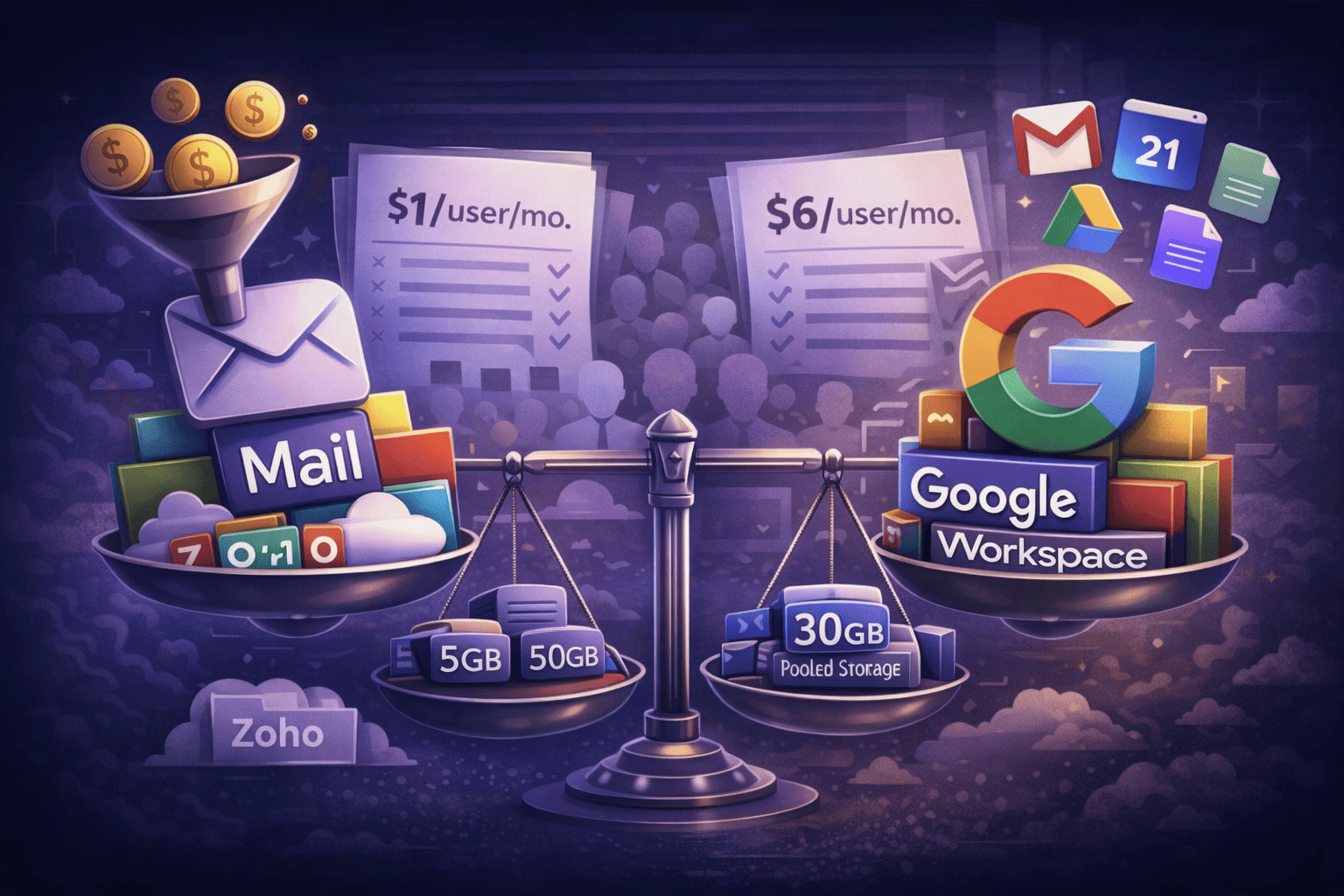
Old Way vs New Way for operators managing lots of domains
The old way to handle dmarc fail was to keep stacking tools until nobody knew which system signed what. The new way is to separate mailbox hosting, delivery, and DNS health clearly so failures are visible and fixable.
| Old Way | New Way |
|---|---|
| Per-user mailbox billing pushes teams into aliases and forwarding hacks | Flat-rate multi-domain hosting keeps real mailboxes affordable |
| One giant SPF record for every service ever added | Clean DNS, fewer includes, and separate subdomains where needed |
| ESP signs with vendor domain | Every sender aligns with your domain |
| No visibility until users complain | DNS health checks catch issues before they become tickets |
| Mailbox moves done by exports and guesswork | Built-in IMAP migration shortens cutovers and reduces auth drift |
That’s the practical TrekMail angle. You can host mailboxes for many domains in one place, use pooled storage instead of per-user fees, and keep outbound flexible with managed SMTP or your own provider. If you’re comparing operating models, see multi domain email hosting and the migration angle in imapsync.
What to do when a DMARC fail ticket lands in your queue
When a dmarc fail ticket shows up, don’t start by changing policy from reject back to none. Start by proving whether the failure came from forwarding, broken DKIM, or bad alignment.
- Get full headers from the recipient.
- Check whether SPF failed because the sending IP belongs to a known forwarder.
- Check whether DKIM passed, failed, and which
d=domain signed. - Check whether the signing domain aligns with the visible From domain.
- Look for
arc=passif the message crossed a trusted intermediary. - Review your SPF record for lookup bloat or stale includes.
If you host mail on TrekMail, the useful starting points are Adding a Domain for record review and I’m Not Receiving Emails when the symptom is a silent miss rather than a visible bounce.
Conclusion: DMARC fail is usually a design problem, not a mystery
A recurring dmarc fail is usually not proof that email is broken beyond repair. It means your setup depends on SPF too much, your DKIM is misaligned or fragile, or your forwarding chain is rewriting mail without preserving trust.
The fix for recurring dmarc fail is boring, which is why it works. Sign with your domain. Keep DKIM durable. Keep SPF sane. Expect forwarding to happen. Build for it.
If you want the easy version of that operating model, TrekMail gives you flat-rate multi-domain mailbox hosting, pooled storage, built-in IMAP migration, catch-all support, and flexible sending without the per-user tax. Paid plans start at $3.50/month billed yearly, there’s a 14-day free trial for paid plans, and the Nano plan stays free with no card required. See pricing or go straight to TrekMail.
The short version is this: if forwarding exists in your environment, dmarc fail is not an edge case. It’s the test. Pass that test, and the rest of your mail stack gets a lot more reliable.