A DMARC analyzer is only useful if it helps you answer one hard question fast: is this domain actually broken, or are you just looking at normal email behavior? If you’re already running business email, start with the bigger operating model in business email. Then use this guide to turn raw DMARC data into decisions you can defend.
The problem is simple. DMARC reports look technical, noisy, and a little threatening. One red row in a dashboard and people start changing SPF, forcing -all, or blaming the mail host. That’s how you break forwarding, miss vendor traffic, and make a small DNS issue much worse. A good dmarc analyzer doesn’t just show failures. It tells you which ones matter, which ones are expected, and what to change first.
This guide covers exactly that: how a dmarc analyzer works, what to look for in aggregate reports, how to separate spoofing from forwarding, and how to fix SPF, DKIM, and alignment problems without taking down legitimate mail.
What is a DMARC analyzer?
A dmarc analyzer collects DMARC aggregate reports, parses the XML, groups sending sources by IP and domain, and shows whether your mail passed SPF, DKIM, and alignment. The point is not the dashboard. The point is finding unauthorized senders and fixing legitimate ones before receivers start junking your mail.
DMARC itself is defined in RFC 7489. It lets the domain owner publish a policy and receive reports about messages using that domain in the visible From address. Those reports usually arrive daily from major receivers like Google, Microsoft, Yahoo, and others.
A dmarc analyzer turns those XML attachments into something an operator can act on:
- Which IPs sent mail claiming to be your domain.
- Whether SPF passed.
- Whether DKIM passed.
- Whether either one aligned with the From domain.
- Whether the receiver applied your DMARC policy.
If you skip the analyzer and read raw XML by hand, you can do it. You’ll also waste hours and miss patterns.
What a DMARC analyzer should tell you first
The first job of a dmarc analyzer is triage. It should help you label each source as legitimate, forwarded, misconfigured, or malicious. If it can’t do that quickly, it’s a pretty graph generator, not an operations tool.
Most failures fall into four buckets.
| What you see in the DMARC analyzer | What it usually means | What to do |
|---|---|---|
| SPF fail, DKIM pass, DMARC pass | Forwarding or relay path changed the sending IP | Usually leave SPF alone and verify DKIM is stable |
| SPF pass, DKIM fail, DMARC pass | Mail is still authentic because SPF aligned | Fix DKIM if possible, but this is not urgent |
| SPF fail, DKIM fail, DMARC fail | Either spoofing or a real sender you forgot to authorize | Identify the source before changing DNS |
| Large volume from unknown IPs or countries | Domain abuse or spoofing attempts | Keep enforcement on and monitor patterns |
This is where beginners get trapped. They treat every SPF failure as a deliverability bug. That’s wrong. TrekMail’s own troubleshooting docs state the core rule plainly: SPF fail plus DKIM pass is often expected in forwarding scenarios, and DMARC can still pass. That’s exactly why your dmarc analyzer has to show alignment, not just raw authentication results.
How to read a DMARC analyzer without chasing ghosts
Read a dmarc analyzer in this order: domain policy, message volume, source IP, SPF result, DKIM result, alignment result, then disposition. If you start with the red icons, you’ll end up fixing the wrong thing.
Here’s the practical workflow.
1. Check your published DMARC record
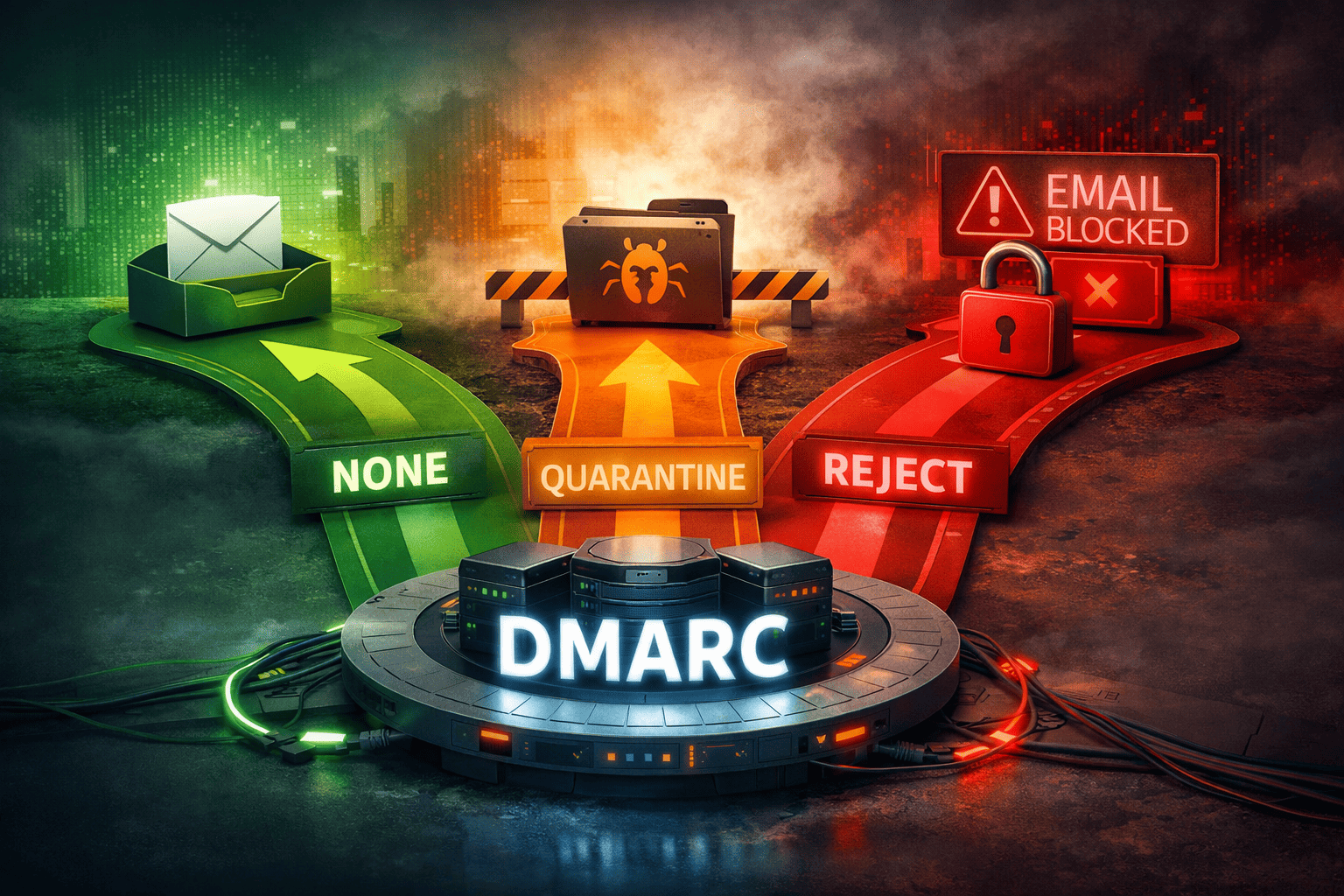
If the domain is publishing p=none, the dmarc analyzer is in observation mode. You’re collecting evidence, not blocking anything yet.
_dmarc.example.com. TXT "v=DMARC1; p=none; rua=mailto:dmarc@example.com; adkim=r; aspf=r; pct=100"If the domain is already at p=quarantine or p=reject, then the analyzer is not just a report reader. It is your early-warning system.
2. Sort by volume first
A random spoofing attempt with three messages matters less than your CRM failing on 12,000 messages a day. The dmarc analyzer should make high-volume sources obvious.
3. Label every known sender
Your real senders usually include your mailbox host, marketing platform, transactional platform, accounting tool, support desk, and anything else allowed to use your domain. If you don’t maintain that list, your analyzer will always feel chaotic.
If you’re still setting up the stack, TrekMail’s DNS guides for required DNS records and checking DNS status are the right baseline before you start interpreting DMARC noise.
4. Look at alignment, not just pass/fail
Google’s sender guidance is explicit: for bulk senders, the organizational domain in the From header must align with either SPF or DKIM. Both SPF and DKIM should exist, but only one needs to align for DMARC to pass.
That one detail explains a lot of confusing analyzer output.
Example: Mail is sent from
billing.example.comthrough a provider whose SPF passes onbounce.vendor.net. SPF passes technically, but it does not align withexample.com. If DKIM is also missing or signed by the wrong domain, DMARC fails.
Common failures a DMARC analyzer exposes
A dmarc analyzer is most useful when it shows failure patterns, not isolated rows. The common patterns are missing SPF includes, broken DKIM, bad domain alignment, forwarding side effects, and duplicate or bloated DNS records.
Missing legitimate sender in SPF
This is the classic case. Your form plugin, invoicing app, or marketing tool sends mail as your domain, but nobody added it to SPF.
dig txt example.com +short
# bad: two separate SPF records
"v=spf1 include:_spf.google.com ~all"
"v=spf1 include:spf.trekmail.net ~all"
# good: one merged SPF record
"v=spf1 include:_spf.google.com include:spf.trekmail.net ~all"If you use TrekMail managed sending, TrekMail’s docs show the required SPF include. If you’re on the Nano plan or want tighter control, TrekMail also supports BYO SMTP. That matters because the real fix depends on which platform is actually sending. See managed TrekMail SMTP and custom SMTP / BYO before touching DNS.
Broken DKIM
Your dmarc analyzer may show SPF passing and DKIM failing for all or most traffic from one vendor. That usually means the selector is wrong, the key was rotated badly, or the vendor is signing with the wrong domain.
This gets serious when forwarding enters the picture. SPF often breaks during forwarding because the connecting IP changes. DKIM is what saves you. ARC can preserve authentication history in complex relays, but you should still treat DKIM as the first line of defense for forwarded mail. The ARC protocol is documented in RFC 8617.
Forwarding noise mistaken for failure
A smart dmarc analyzer helps you spot forwarding fast. Look for consumer ISP IPs, university systems, or large mailbox providers appearing as the source while DKIM still passes.
If forwarding is part of your setup, read TrekMail’s email forwarding guide and forward domain email to Gmail. This is one of the easiest places to cause silent delivery damage by “fixing” the wrong layer.
SPF lookup bloat
Some analyzers surface SPF PermError cleanly. Some don’t. Either way, if your SPF chain goes past the 10-DNS-lookup limit, you’re in trouble. That can make legitimate traffic fail even though the vendor is authorized on paper.
The answer is not to pile on more includes. Remove dead services. Replace what you can with static ip4 entries. Split high-volume senders onto subdomains when it makes sense.
What the best DMARC analyzer tools do better than the rest
The best dmarc analyzer tools don’t win on prettier dashboards. They win on classification, alerting, and operational context. You need to know what changed, which sender is new, and whether it’s safe to enforce policy harder.
After reviewing live competitors, the pattern is obvious. Most tools promise the same five things: XML parsing, pass/fail charts, alerts, compliance scoring, and sender discovery. That’s table stakes now.
The gaps are where good operators care:
- Can the tool separate forwarding from spoofing without drama?
- Can it tell you whether a source is worth fixing based on volume?
- Can it map failures back to your actual sending stack?
- Can it warn you when SPF bloat or alignment drift is about to hurt delivery?
That’s also where TrekMail fits the bigger workflow better than a standalone analyzer subscription for many teams.
Old way vs new way
The old way is buying one more SaaS just to parse XML, then fixing DNS manually across a pile of domains, mail hosts, and sending vendors. The new way is running a standards-first mail stack where DNS health, SMTP choice, forwarding behavior, and migration live in one place.
| Old way | New way with TrekMail |
|---|---|
| Per-user mailbox pricing even when you manage many domains | Flat-rate multi-domain hosting with pooled storage |
| Separate analyzer, separate mailbox host, separate migration workflow | One dashboard for domains, mailboxes, DNS checks, forwarding, and IMAP migration |
| Blindly switch SPF or DMARC because reports look scary | Verify DNS, confirm sender path, then fix the exact source |
| Forwarding breaks and nobody can explain why | Standards-first setup with SRS forwarding support and clear DNS guidance |
For solo founders and small teams, this means fewer moving parts. For agencies and MSPs, it means less margin lost to mailbox sprawl and DNS accidents. TrekMail starts with a Nano plan at $0 for 10 domains and 5GB, then paid plans start at $3.50/month. If you need managed sending, a 14-day paid trial is available with a credit card. If you don’t, the Nano plan is always free and supports BYO SMTP.
If your real pain is multi-domain sprawl, read multi domain email hosting. That’s where a lot of DMARC mess actually starts.
How to fix what your DMARC analyzer shows
The fix path depends on whether the source is real, forwarded, or hostile. A dmarc analyzer gives you the evidence. You still need a decision tree so you don’t make the problem worse.
- If the source is your real vendor, authorize it and verify alignment.
- If the source is a forwarder, leave SPF alone and make sure DKIM survives.
- If the source is unknown, keep or move toward enforcement.
- If both SPF and DKIM fail for your own mail, stop sending from that source until it’s fixed.
For live checks, use your terminal instead of stale web checkers:
dig txt _dmarc.example.com +short
dig txt example.com +short
# inspect a DKIM selector
dig txt selector1._domainkey.example.com +shortIf your domain is hosted on TrekMail, confirm that DNS status is green before you dig into deliverability blame. TrekMail’s emails go to spam guide also calls out the operational reality: missing authentication and poor reputation are the usual causes, not mystery filtering.
When to move from p=none to p=quarantine or p=reject
A dmarc analyzer helps you earn enforcement. Don’t move to p=reject because it sounds tougher. Move when your legitimate senders are known, aligned, and stable.
There’s no prize for publishing p=reject too early. You just create a higher-speed failure. The right progression is still the boring one:
- Start with
p=noneand collect reports. - Fix authorized senders until the report is clean enough to trust.
- Move to
p=quarantine. - Watch the dmarc analyzer for at least a full reporting cycle.
- Then move to
p=reject.
Google’s current sender FAQ, updated through 2025 and 2026 guidance, makes the enforcement trend clear. For bulk senders to personal Gmail accounts, missing DMARC, failed SPF, failed DKIM, or broken alignment can now trigger rate limits, spam foldering, and hard blocks. If you’re sending volume, this is not optional work anymore.
Conclusion: use a DMARC analyzer to make decisions, not panic
A good dmarc analyzer does not exist to scare you with red bars. It exists to show which sources are legitimate, which failures are expected, and which issues need a DNS or sender-path fix right now. If your analyzer can’t separate spoofing, forwarding, and bad configuration, it’s not helping.
That’s also why TrekMail is useful beyond mailbox hosting. You can run custom domains, IMAP mailboxes, catch-all routing, mailbox forwarding, built-in IMAP migration, and either managed SMTP or BYO SMTP from one standards-first setup. Less glue. Less guessing. Fewer places for DMARC to break.
If you want to tighten your stack without paying per-user tax, start at trekmail.net or compare plans at trekmail.net/pricing. And if you’re using a dmarc analyzer today, use it the way an operator would: classify, verify, fix, then enforce.