You bought a custom domain. You want hello@yourdomain.com to land in your Gmail. That's it. No second inbox, no per-seat license, no fuss. Email forwarding custom domain setup sounds like a five-minute job—until your messages start vanishing or landing in spam. The problem isn't the concept. It's that forwarding fights against the very protocols designed to protect your inbox.
This guide breaks down how to set up email forwarding on a custom domain the right way in 2026, the DNS mistakes that silently kill delivery, and how to verify everything actually works. If you want the deep technical background on SRS and ARC, read our pillar guide on email forwarding setup and troubleshooting.
How Email Forwarding Custom Domain Setup Works
Email forwarding custom domain configuration routes incoming messages from your domain's address to an existing mailbox (like Gmail or Outlook) without storing them locally. Your forwarding provider acts as a relay—it receives the message and immediately passes it on to your destination inbox.
There are two architectural patterns for email forwarding custom domain routing, and picking the right one determines your reliability, cost, and headache level.
Provider-Level Routing (MTA Forwarding)
The forwarding provider's mail server receives the message and redirects it instantly. No local mailbox, no storage fees. This is the standard approach in 2026 and the one services like TrekMail use. It scales to hundreds of aliases without per-user costs.
Mailbox Rule Forwarding
You pay for a full mailbox (Google Workspace, Microsoft 365) and create a forwarding rule inside it. This costs $6–$30/month per user, breaks when the license expires, and often triggers outbound spam blocks. It's the legacy path—avoid it unless you need granular server-side filtering.
| Feature | Provider-Level Routing | Mailbox Rules |
|---|---|---|
| Cost | Flat rate or free | Per-user monthly fee ($6–$30) |
| Point of Failure | DNS / MX records | User login / license / client rules |
| SPF & DKIM | Managed by provider (SRS) | Often breaks DMARC alignment |
| Scalability | 100+ aliases instantly | Manual setup per user |
| Catch-All Support | Built-in with spam controls | Limited or unavailable |
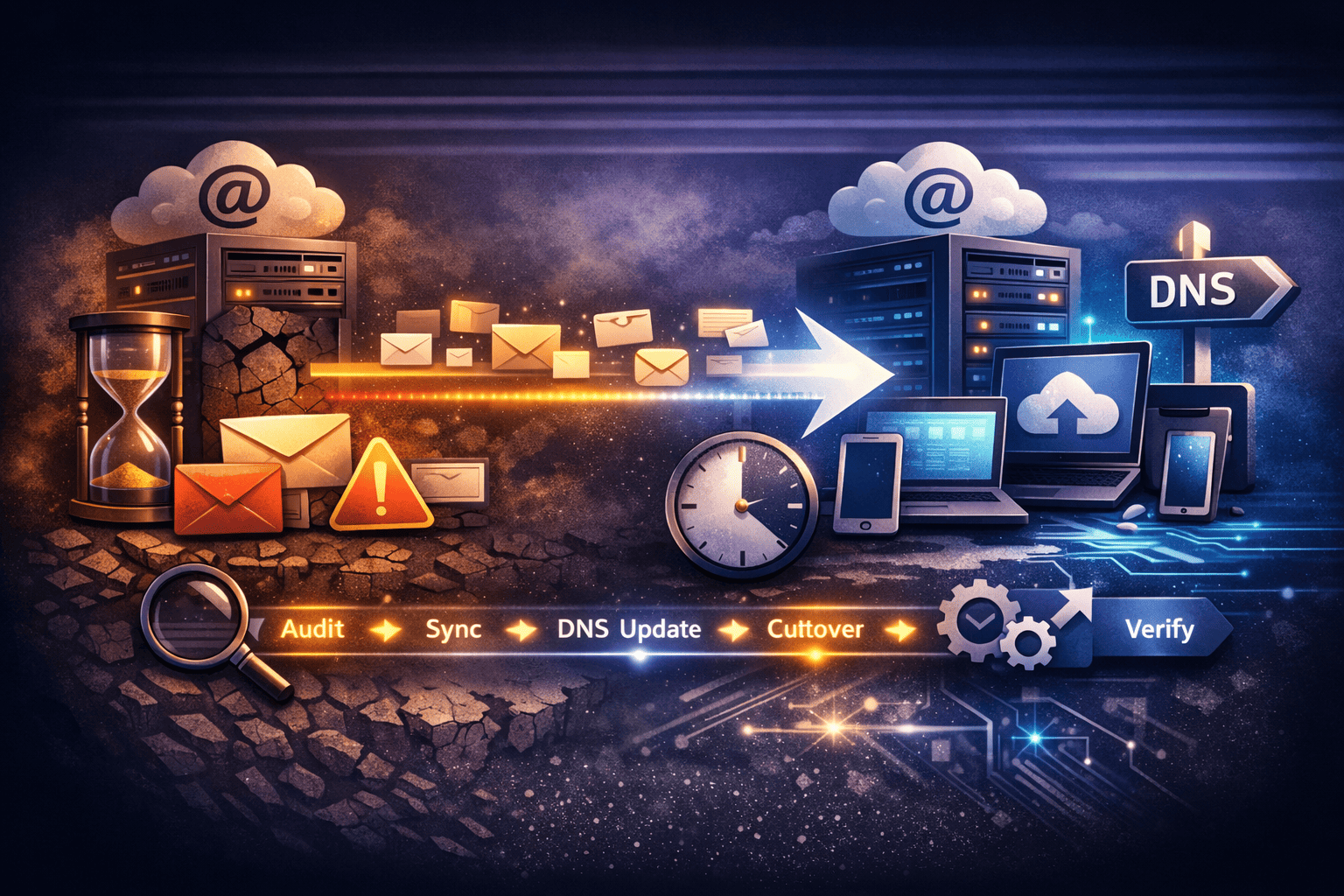
Step-by-Step: Set Up Email Forwarding on Your Custom Domain
A proper email forwarding custom domain configuration takes four steps. Each one matters. Skip the DNS propagation check and you'll spend hours debugging something that would've fixed itself in 15 minutes.
Step 1: Verify Domain Ownership
Your forwarding provider needs proof you own the domain. You'll add a TXT record to your DNS. Something like:
trekmail-verify=abc123def456This record tells the provider “yes, the person configuring forwarding actually controls this domain.” Don't remove it after verification—some providers recheck periodically.
Step 2: Configure MX Records
MX (Mail Exchange) records tell the internet where to deliver email for your domain. You can only have one active email provider at a time. Delete all old MX records before adding new ones. Leftover records from a previous host cause split delivery—some messages hit the old server and bounce.
@ MX 10 mx1.trekmail.net
@ MX 20 mx2.trekmail.net
Step 3: Create Your Forwarding Route
In your provider's dashboard, map the source address to the destination:
info@yourdomain.com → yourname@gmail.com
Want to forward your domain email to Gmail specifically? The setup is the same—just make sure you don't test by sending from the destination address back to yourself (Gmail silently discards these “hairpin” messages).
Step 4: Add the SPF Record
This is the step people skip, and it's the reason their forwarded email lands in spam. An SPF record authorizes your forwarding provider to send mail on your domain's behalf.
v=spf1 include:_spf.trekmail.net ~allWithout this, the destination server sees an unauthorized IP sending mail for your domain, and that's a one-way ticket to the junk folder.
5 DNS Mistakes That Kill Email Forwarding Custom Domain Setups
Most email forwarding custom domain failures trace back to DNS errors. These are the five that generate the majority of support tickets across the industry.
1. Mixed MX Records (“Split Brain”)
Leaving old MX records (like ASPMX.L.GOOGLE.COM) alongside your new provider's records causes random delivery. Some emails hit Google (and bounce because no mailbox exists), some reach your forwarder. Fix: Delete every MX record that doesn't belong to your active provider.
2. Missing or Incorrect SPF (“Softfail Trap”)
Forwarding changes the sending IP. If your SPF record doesn't include the forwarder, the destination server flags it. You'll see emails arrive but marked as spam, sometimes with a red question mark icon in Gmail.
3. CNAME on the Root Domain
Some registrars offer CNAME-based “easy setup,” but a CNAME on the root domain (@) violates RFC 1034 and breaks MX resolution. Use A records for your website and MX records for email. Never CNAME the apex.
4. Phantom Local Mailbox
Migrating away from a shared host (Bluehost, GoDaddy, etc.) but leaving “Local Mail Exchanger” enabled in cPanel? The server intercepts mail before it reaches external DNS. Your test email works (because you sent it from the same server), but external senders get “User Unknown” bounces.
5. Catch-All Conflicts
Setting up a specific forward for info@ alongside a catch-all for *@ can create routing loops if the provider doesn't prioritize correctly. This triggers 5.4.6 or 554 5.4.14 hop count exceeded errors. Define specific aliases first. Use catch-alls sparingly—they're spam magnets.
The Verification Plan: Don't Assume It Works
After completing email forwarding custom domain setup, run a three-phase test before calling it done. “No error message” doesn't mean it's working.
Phase 1: External Sender Test
Send a test email from a third-party account (Yahoo, Proton, a friend's address). Don't send from your Gmail to your forwarding address that routes back to Gmail—Google silently drops these hairpin messages.
Phase 2: Reply-To Test
When the forwarded email arrives, hit Reply. The “To” field should show the original sender's address, not your forwarding address. If it shows info@yourdomain.com, your provider is rewriting headers incorrectly.
Phase 3: Header Inspection
Open the raw message source and look for Authentication-Results:
Authentication-Results: mx.google.com;
dkim=pass header.i=@original-sender.com;
spf=pass (domain of SRS0=... designates ... as permitted sender)
That SRS0 reference in the SPF line confirms Sender Rewriting Scheme is active. If you see spf=softfail or dmarc=fail, your DNS needs work.
Why Email Forwarding Breaks (and How to Fix It)
Email forwarding custom domain setups break in predictable ways. Knowing the failure modes saves you hours of guessing.
The DMARC Double Failure
This is the #1 reason forwarded emails silently disappear. A sender with a strict DMARC policy (p=reject) sends you a message. Your forwarder changes the IP (breaking SPF). If it also modifies the subject or body—adding a disclaimer, for example—DKIM breaks too. SPF fail + DKIM fail = DMARC reject. The message vanishes with no bounce notification to you.
Microsoft 365 Outbound Block (5.7.520)
Microsoft's default security policies can break email forwarding custom domain setups by blocking external forwarding. If you're forwarding from an M365 mailbox, you'll get 550 5.7.520 Access denied, your organization does not allow external forwarding. Fix: Edit the Outbound Spam Filter Policy in Microsoft Defender to allow automatic forwarding.
Out-of-Office Loops
User A forwards to User B. User B has auto-reply on. The auto-reply gets forwarded back, triggering another auto-reply. Thousands of messages flood the system in minutes. Modern servers use X-Auto-Response-Suppress headers to prevent this, but older setups still melt down.
| Symptom | Likely Cause | Fix |
|---|---|---|
NDR 5.7.1 or 5.7.26 | SPF / authentication failure | Add forwarder to SPF record; check IP reputation |
NDR 5.4.6 or 5.4.14 | Routing loop | Check for circular forwarding rules (A → B → A) |
| No email, no bounce | DMARC reject / spam filter | Check spam folder; inspect headers for dmarc=fail |
M365 5.7.520 | Outbound policy block | Edit Defender Outbound Spam Filter settings |
| Email arrives but looks broken | DKIM signature invalidated | Forwarder modified content; check dkim=fail in headers |
| Reply goes to wrong address | Reply-To header rewritten | Verify forwarding preserves original Reply-To |
Outlook 421 4.7.26 | Rate limiting / reputation throttle | Temporary block; check forwarder's domain reputation |
SRS and ARC: The Protocols That Make Forwarding Work
Two protocols keep email forwarding custom domain routing alive in 2026 and prevent silent delivery failures. Without SRS and ARC, any email forwarding custom domain setup is essentially broken against modern spam defenses.
SRS (Sender Rewriting Scheme)
SRS rewrites the envelope sender so SPF checks pass at the destination. When your forwarder receives mail from alice@bank.com, it rewrites the envelope to something like SRS0=hash=timestamp=bank.com=alice@forwarder.com. The destination server validates SPF against the forwarder's domain (which passes), and bounce messages still route back to Alice.
ARC (Authenticated Received Chain)
SRS fixes SPF, but DMARC alignment can still fail. ARC lets the forwarder cryptographically sign the message, attesting: “I verified authentication when I received this.” Major providers like Google and Microsoft trust ARC seals to override DMARC failures. As described in RFC 8617, ARC creates a chain of custody that preserves authentication results across hops.
The Catch-All Danger Zone
When using email forwarding custom domain routing, a catch-all inbox (*@yourdomain.com) paired with forwarding is tempting but dangerous. Every piece of spam hitting any random address at your domain gets forwarded to Gmail or Outlook. Those providers see your domain as the source of that spam. Your domain reputation tanks. Your IP gets blocklisted. Eventually, even legitimate forwarded mail stops arriving.
If you need a catch-all, use a provider that filters spam before forwarding. TrekMail's catch-all inbox, for example, applies reputation checks at the MX level so junk never reaches your destination.
When to Stop Forwarding and Get a Full Mailbox
Email forwarding custom domain routing handles inbound delivery. It doesn't replace a mailbox. Switch to a hosted mailbox if:
- You need to send outbound mail as your domain. Gmail's “Send As” feature works but is increasingly restricted. A proper mailbox with authenticated SMTP is more reliable.
- Volume exceeds 500 messages/day. Gmail and Outlook rate-limit forwarded traffic. High-volume senders need direct delivery.
- Compliance requires it. HIPAA or GDPR data passing through a third-party forwarder adds an uncontrolled processing hop. That's a liability.
For most small businesses, freelancers, and agencies, email forwarding custom domain routing covers 90% of the use case. You don't need 10 mailbox licenses just to route info@, support@, and billing@ to the same Gmail.
TrekMail: Email Forwarding Built for Custom Domains
Managing email forwarding custom domain routing by hand means wrestling with MX records, SPF includes, SRS configuration, and cryptic bounce codes. It's grunt work.
TrekMail handles the infrastructure so you don't have to. SRS, ARC, SPF/DKIM/DMARC wizard, catch-all filtering, multi-domain dashboard—it's all built in. Whether you run one domain or a thousand, pricing stays flat:
- Free Plan: $0/month — 10 domains, 5GB storage, BYO SMTP
- Starter: $3.50/month — 50 domains, 15GB storage
- Pro: $10/month — 100 domains, 50GB storage
- Agency: $23.25/month — 1,000+ domains, 200GB+ storage
The Nano plan is always free—no trial, no credit card. Paid plans include a 14-day free trial. Get started with TrekMail and stop paying per-user fees for something that should be a utility.
Conclusion: Get Email Forwarding Custom Domain Setup Right
Email forwarding custom domain routing isn't a “set and forget” checkbox. It's an active routing layer that demands correct DNS, modern authentication (SRS + ARC), and proper verification. Get the MX records right, add your SPF include, test with an external sender, and inspect those headers.
The five DNS mistakes above account for the vast majority of email forwarding custom domain failures. Fix those first. If you want a provider that handles the hard parts automatically, TrekMail was built for exactly this. Stop losing emails. Start routing them properly.