Your emails land in spam. You switch hosting providers. Still spam. You get a fresh dedicated IP. Still spam. You rebuild the server from scratch. Still spam.
Here's what nobody says upfront: the problem isn't your server. It's your domain name.
Domain reputation email metrics attach to your root domain — company.com — not the infrastructure you send from. Swap hosts, rotate IPs, migrate to a new provider. The taint follows you, because it's your domain name that's flagged, not your server. Changing your mailing address doesn't clear your name from the list.
If you're still building the foundation — DNS setup, mailbox configuration, authentication basics — the business email for small business guide covers all of that. This article is about one specific failure mode: domain taint. Why it happens, which error codes confirm it, and the architecture that prevents it.
What Is Domain Reputation Email?
Domain reputation email is the trust score mailbox providers — Google, Yahoo, Microsoft — assign to your sending domain. It's built from spam complaint rates, authentication pass rates, engagement patterns, and sending volume history. Unlike IP reputation, domain reputation email is permanently bound to your domain name. You can't reset it by switching providers or rotating servers.
In 2025–2026, domain reputation carries more weight than IP reputation for major providers. Google and Yahoo built domain-level tracking specifically because operators learned to evade IP-based filters by rotating addresses. The domain became the stable identity to track — so that's what they now target.
This matters for domain reputation email in a specific way: you can do everything right at the server level — clean IP, proper PTR records, low bounce rates — and still get blocked because of your domain's history. Domain reputation is the ceiling. Everything else is a floor.
What "Tainted" Looks Like: Diagnostic Symptoms
Domain reputation email damage shows up as specific rejection patterns, not content issues. Mail gets accepted then immediately junked, blocked at the gateway with 550 errors, misrouted to Promotions, or blocked on brand-new IP addresses. Each symptom points to a different failure mode — the right fix depends on which one you're seeing.
| Symptom | Technical Signature | Diagnosis |
|---|---|---|
| Emails default to Spam | 250 OK — accepted, then junked | Reputation degradation. Receiver accepts but distrusts the domain. |
| Policy rejection at gateway | 550 5.7.1 or 550 5.7.515 (Microsoft) | DMARC failure or low reputation. Message rejected before the inbox. |
| Transactional mail in Promotions | Invoices and resets land in Gmail Promotions | Google has classified your domain as a marketing sender due to mixed traffic. |
| Immediate block on fresh IP | Brand-new dedicated IP, blocked day one | Domain taint confirmed. The IP is neutral — the block comes from the domain name alone. |
That last row is the definitive test. A fresh IP has zero history — no good signals, no bad ones. If it gets blocked immediately after you point it at your domain, the taint lives in the domain itself. No infrastructure swap fixes domain reputation email damage at this level.
The Four Operational Causes of Domain Taint
Sophisticated filters don't block domains for spammy words. They block them for behavioral and infrastructure patterns. Understanding these four causes is the first step to protecting your domain reputation email from permanent damage.
1. Subdomain Reputation Aggregation
A common myth: "I'll send risky campaigns from promo.example.com so example.com stays clean."
It doesn't work. Google aggregates reputation at the organizational domain level. If promo.example.com generates a high complaint rate, the taint flows upstream to example.com. Subdomains provide some signal separation — they're not a firewall for domain reputation email damage.
2. The Bulk-Sender Threshold (The Permanence Trap)
Since February 2024, Google and Yahoo apply stricter compliance requirements to "Bulk Senders" — domains that send roughly 5,000+ emails per day to Gmail or Yahoo addresses.
The trap: once your domain crosses this threshold even once — say, a Black Friday blast — it's permanently tagged as a Bulk Sender. Your volume drops back to 50 emails a day. You're still held to bulk-sender standards: DMARC enforcement, one-click unsubscribe, strict list hygiene. Forever.
3. The 0.3% Complaint Cliff
Google and Yahoo enforce a hard ceiling on spam complaint rates:
- Threshold: 0.3% (3 complaints per 1,000 emails)
- Where to check: Google Postmaster Tools — the only authoritative view of your domain reputation email score with Gmail
- Recovery timeline: 30–60 days of near-perfect sending behavior after dropping below the threshold
Most operators don't know they're near the cliff until they've already fallen off it. Set up Google Postmaster Tools before you have a problem — not after.
4. The Noisy Neighbor Effect (Shared IPs)
Standard shared hosting — cPanel, cheap webmail plans — sends your mail from an IP shared with hundreds of other tenants. One neighbor runs a phishing campaign. The IP hits Spamhaus SBL. While this is technically an IP reputation issue, repeated association with dirty shared IPs degrades your domain reputation email score over time. The line between IP and domain reputation blurs when you've been burned from the same pool repeatedly.
Prevention: The Clean Domain Architecture
Clean domain reputation email requires three layers working together: proper authentication, traffic isolation across separate root domains, and verified network infrastructure. Skip any one layer and you're exposed. None of this is optional if you send at any meaningful volume.
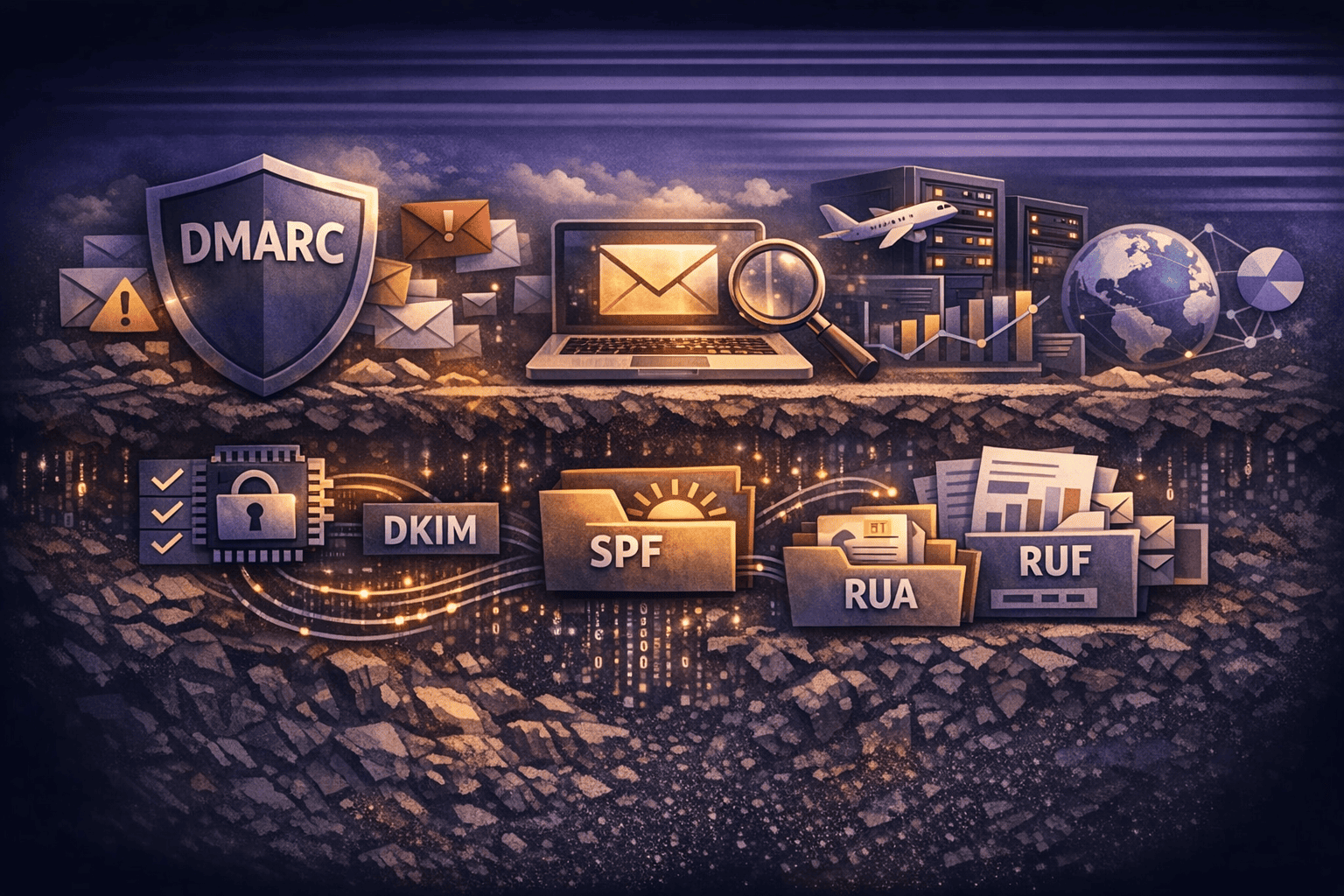
Layer 1: Authentication — SPF, DKIM, DMARC
Authentication is non-negotiable. Without it, receivers can't verify you sent the message — and they won't trust you.
- SPF: Authorizes which IPs can send for your domain. Watch the 10-lookup limit — too many vendor includes (Google Workspace, Mailchimp, Zendesk) causes a PermError that breaks SPF entirely.
- DKIM: Signs each message cryptographically. Use 2048-bit keys minimum.
- DMARC: Enforces receiver policy on messages that fail SPF or DKIM. Start at
p=noneto monitor, then move top=quarantineorp=reject.
# Example DMARC record — replace with your reporting address
_dmarc.company.com TXT "v=DMARC1; p=quarantine; rua=mailto:dmarc@company.com; pct=100"Missing DMARC enforcement is the primary trigger for the 550 5.7.515 rejection at Microsoft. It's also required for bulk senders under the 2024 Google/Yahoo mandate. If you're seeing that error code, check your DMARC policy first.
Layer 2: Domain Isolation (Cousin Domains)
Don't send cold outreach or high-volume marketing from your primary corporate domain. Use completely separate root domains.
Primary: company.com — CEO correspondence, invoices, customer support. Zero marketing traffic.
Marketing: trycompany.com — newsletters, product updates.
Outreach: getcompany.com — cold email sequences.
If getcompany.com hits a spam trap and burns, your CEO can still email investors from company.com. This is the only structure that provides actual protection to your primary domain reputation email. For agencies deploying this across dozens of clients, the multi-domain email hosting guide covers provisioning at scale.
Layer 3: Network Hygiene — FCrDNS
Your sending IP needs a valid PTR record (reverse DNS) that resolves back to your hostname. This is Forward-Confirmed reverse DNS (FCrDNS).
# Verify FCrDNS on your sending IP
dig -x YOUR_IP_ADDRESS # Should return your hostname
dig +short YOUR_HOSTNAME # Should return the same IPIf those don't match, Gmail and Microsoft treat it as an immediate block signal. Fix this before warming up any new IP.
Layer 4: Warm-Up and Inactivity Decay
Domain reputation email is not static — it decays without consistent, clean activity.
- New domain: Start at 20 emails on day one. Double every 2–3 days. No cold outreach for the first 30 days.
- Inactive domain: If a domain stops sending for more than 30 days, its reputation resets. Re-warm it from scratch as if it were new.
TrekMail's domain warmup rules spell out the exact ramp schedule for managed SMTP accounts.
Immediate Remediation: If You're Already Tainted
If your domain reputation email is already damaged — open rates under 5%, hard bounces climbing, 550 rejections even on clean IPs — the recovery protocol is the same regardless of how you got there. Execute it in order, not in parallel.
- Stop all promotional traffic immediately. Send only transactional email — password resets, receipts — to your highest-engagement users. Nothing else until reputation improves.
- Audit Google Postmaster Tools. This is the only authoritative view of your domain's reputation with Gmail. If it shows "Bad," plan for a 4–8 week recovery window and set realistic expectations with stakeholders.
- Purge unengaged contacts. Delete anyone who hasn't opened an email in 90 days. You need to artificially inflate your engagement rate to signal value to mailbox providers.
- Migration — the nuclear option. If your domain is permanently listed on Spamhaus DBL with no removal path, you're not recovering it. Abandon it for email, migrate to a new domain, and build the architecture correctly from day one. The set up email on my domain guide covers the full technical setup for a clean start.
How TrekMail Enforces This by Default
Most SMBs and agencies damage their domain reputation email for the same reason: they mix traffic streams on cheap infrastructure. CEO correspondence and newsletter blasts share the same server. One blast-and-burn campaign taints the whole domain.
TrekMail builds the correct architecture in from the start.
| The Old Way | The TrekMail Way |
|---|---|
| CEO mail and newsletters share a server | Corporate mail on managed, clean IP pools |
| Shared hosting with unknown IP neighbors | BYO SMTP for bulk sending (SES, SendGrid, Mailgun) |
| One domain for everything | Multi-domain provisioning — isolate traffic by function |
| Manual DNS setup, errors expected | SPF/DKIM/DMARC wizard on every domain onboarded |
For SMBs, TrekMail hosts your corporate email (team@company.com) on managed IPs with authentication configured out of the box. For bulk sending, TrekMail supports BYO SMTP — Amazon SES, SendGrid, Mailgun. Your CEO's mail stays on clean infrastructure. Marketing volume routes through an engine built for it. The separation is enforced at the infrastructure level, not as a policy you have to remember.
For agencies, you can provision this architecture across 100+ client domains from a single dashboard. Each client gets a clean corporate inbox. Their marketing traffic routes through a separate relay. When a client campaign hits a spam trap, it doesn't touch their primary domain — or your reputation as their provider. The client email management guide covers how agencies structure this across accounts.
Domain reputation email damage is one of the few problems in email where the fix is architectural, not tactical. Authentication, domain isolation, clean infrastructure — all three have to be in place before you send at volume.
TrekMail's Starter plan starts at $3.50/month with managed SMTP, SPF/DKIM/DMARC setup, and multi-domain support. The 14-day trial gives you full access to test the setup — a credit card is required to activate it. Prefer to start without one? The Nano plan gives you 10 domains and BYO SMTP at $0, no card required, always free.
Once your domain reputation email is clean, keeping it that way is mostly maintenance. But you have to build it right first.