If you're sending email from your own domain, you need to create DKIM record entries in DNS. Knowing how to create DKIM record settings correctly is essential for deliverability. Without one, receiving servers have no way to verify that your messages weren't tampered with in transit. Google, Yahoo, and Microsoft now require DKIM for bulk senders, and even low-volume domains take a deliverability hit without it.
This guide walks through the entire process — generating keys, publishing the DNS record, enabling signing, and verifying everything works. No fluff. Just the steps, the syntax, and the gotchas that trip people up. Whether you create DKIM record entries manually or use a managed platform, the fundamentals to create DKIM record entries are the same.
What Is a DKIM Record?
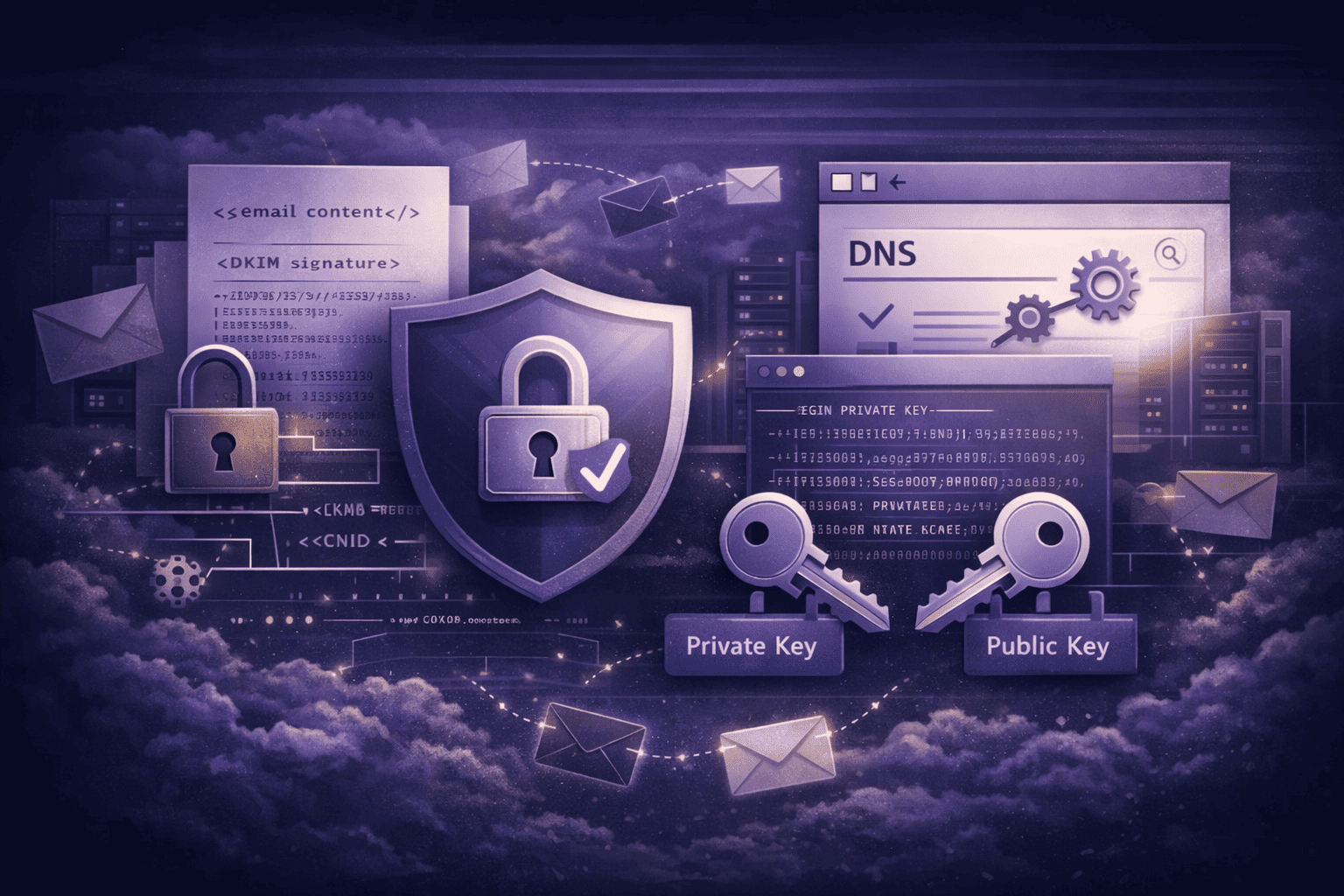
A DKIM record is a DNS TXT entry that holds the public half of a cryptographic key pair. Your mail server signs every outgoing message with the private key. The receiving server fetches the public key from your DNS, checks the signature, and confirms two things: the message actually came from your domain, and nobody altered the body or headers in transit. DKIM is defined in RFC 6376 and it's the backbone of modern email authentication.
How to Create DKIM Record Entries in 4 Steps
Step 1: Generate Your DKIM Key Pair
Before you create DKIM record entries, you need a key pair. Every DKIM setup starts with a key pair — a private key that stays on your mail server and a public key that goes into DNS. How you generate the pair depends on your setup.
If you use a hosted email service (Google Workspace, Microsoft 365, Zoho), the provider generates the keys for you. You just need to copy the DNS record they provide. In Google Workspace, go to Admin Console > Apps > Google Workspace > Gmail > Authenticate Email and click "Generate new record."
If you run your own mail server (Postfix, Exim, OpenDKIM), generate the pair from the command line:
openssl genrsa -out dkim_private.pem 2048
openssl rsa -in dkim_private.pem -pubout -out dkim_public.pemUse 2048-bit keys. Some legacy guides mention 1024-bit, but that key length is considered weak as of 2026. Many receivers now downgrade trust for 1024-bit signatures.
You also need to pick a selector — a label that identifies this specific key. Selectors let you rotate keys or use different keys for different services. Common conventions include google, s1, mail2026, or the service name like sendgrid.
Step 2: Add the Public Key to DNS
This is the step where you actually create DKIM record entries in your domain's DNS. Most providers make it straightforward to create DKIM record values. Log into your DNS provider (Cloudflare, Route 53, GoDaddy, Namecheap) and add a new TXT record.
Host/Name field:
selector._domainkey.yourdomain.comReplace selector with the name you chose in Step 1. If your selector is s1 and your domain is example.com, the full record name is:
s1._domainkey.example.comValue field:
v=DKIM1; k=rsa; p=MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA2K4PavXoNY8eGK2u...truncated...base64encodedpublickeyThe p= tag contains your full public key as a single base64 string. Strip the PEM headers (-----BEGIN PUBLIC KEY-----) and all line breaks — DNS needs it as one continuous string.
Important: Some DNS providers have a 255-character limit per TXT string. If your key exceeds this (2048-bit keys always do), the provider should automatically split it into multiple quoted strings. If it doesn't, you'll need to manually break it into 255-character chunks wrapped in double quotes. The DNS protocol reassembles them.
Step 3: Enable DKIM Signing on Your Mail Server
After you create DKIM record entries in DNS, the record alone doesn't do anything. Your mail server needs to actively sign outgoing messages with the private key.
Google Workspace: Toggle "Start authentication" in the same admin panel where you generated the key.
OpenDKIM (Postfix/Exim): Edit /etc/opendkim.conf:
Selector s1
KeyFile /etc/opendkim/keys/example.com/dkim_private.pem
Domain example.com
Socket inet:8891@localhostThen add the milter to Postfix in /etc/postfix/main.cf:
milter_default_action = accept
milter_protocol = 6
smtpd_milters = inet:localhost:8891
non_smtpd_milters = inet:localhost:8891Restart both services:
sudo systemctl restart opendkim
sudo systemctl restart postfixThird-party senders (SendGrid, Mailgun, Amazon SES) each have their own DKIM activation flow. The pattern is always the same: they give you a CNAME or TXT record, you add it to DNS, then click "Verify" in their dashboard.
Step 4: Verify the Record
Don't assume it's working. Verify immediately.
From the command line:
dig TXT s1._domainkey.example.com +shortYou should see your public key in the response. If you get an empty result, DNS hasn't propagated yet (give it up to 48 hours, though most TXT records propagate in minutes).
By sending a test email: Send a message to a Gmail address and inspect the raw headers. Look for:
Authentication-Results: mx.google.com;
dkim=pass header.i=@example.com header.s=s1If you see dkim=pass, you're done. If you see dkim=fail or dkim=neutral, something is misconfigured — check the next section for common mistakes.
DKIM Record Syntax Explained
When you create DKIM record entries, understanding the syntax matters — especially when you create DKIM record entries for the first time. Here's the full anatomy:
v=DKIM1; k=rsa; t=s; p=MIIBIjANBgkqhkiG9w0BAQE...| Tag | Required | Meaning |
|---|---|---|
v=DKIM1 | Yes | Version. Must be DKIM1. |
k=rsa | No | Key type. RSA is the default and most common. Ed25519 is emerging but not widely supported yet. |
p= | Yes | Public key (base64). An empty p= means the key has been revoked. |
t=s | No | Strict mode — the signing domain must exactly match the From header domain. Without it, subdomains can match. |
t=y | No | Testing mode — receivers shouldn't treat failures differently. Remove this once you're confident everything works. |
Common Mistakes When You Create DKIM Record Entries
When teams create DKIM record entries for the first time, the same mistakes come up repeatedly.
1. Line breaks in the public key. The most frequent issue. If you copy the key from a PEM file and paste it with line breaks into your DNS value field, the record is invalid. Strip all newlines and whitespace from the base64 string.
2. Wrong selector in the DNS name. You generated the key with selector s1 but your mail server config says default. The receiving server looks up default._domainkey.example.com, finds nothing, and DKIM fails. The selector in DNS must exactly match the selector your mail server uses when signing.
3. Multiple DKIM records with the same selector. Unlike SPF (which must have exactly one record per domain), you can have multiple DKIM records — but each must have a unique selector. If you create two TXT records for s1._domainkey, DNS returns both and the receiving server may pick the wrong one.
4. Forgetting to enable signing. You added the DNS record and assumed that was it. The DNS record publishes the public key. Your mail server still has to actively sign every outgoing message with the private key. Without signing, the record just sits there doing nothing.
5. Using 1024-bit keys. They still technically work, but Google's sender guidelines and most security auditors now recommend 2048-bit minimum. Upgrading is straightforward — generate a new key pair, publish the new public key under a new selector, update your mail server config, and revoke the old key by setting its p= value to empty.
DKIM, SPF, and DMARC — The Full Stack
DKIM doesn't work in isolation. It's one leg of a three-part authentication framework.
SPF verifies that the sending server's IP address is authorized by the domain owner. It's essential, but it breaks when email is forwarded because the sending IP changes. If you haven't set up SPF yet, start with our SPF record setup guide — and read up on how SPF works for email to understand the 10-lookup limit and other constraints.
DKIM survives forwarding because the signature is attached to the message content, not the sending IP. That's why it's the critical complement to SPF.
DMARC ties them together. It tells receiving servers what to do when both SPF and DKIM fail — quarantine the message, reject it, or do nothing. DMARC requires at least one of SPF or DKIM to pass and align with the From header domain.
The goal is full alignment: SPF passes and aligns, DKIM passes and aligns, DMARC is set to p=reject. That's the profile of a domain with strong domain reputation, and it's what inbox providers reward with better placement.
If you're running a business, this stack isn't optional. It's the minimum for secure email operations.
How TrekMail Handles DKIM for You
If you only need to create DKIM record settings for a single domain, doing it manually works fine. But when you need to create DKIM record entries across dozens of domains, automation becomes essential. It gets painful at scale — rotating keys, managing selectors across multiple services, catching misconfigurations before they tank your deliverability.
TrekMail's approach: we generate and manage DKIM keys for every domain on the platform. When you connect a domain, the SPF/DKIM/DMARC wizard gives you the exact DNS records to add. Once they're published, we validate them in real time and flag any issues before they affect delivery.
- Nano plan ($0): BYO SMTP (Amazon SES, Mailgun, etc.) — we generate the correct DKIM records for your provider. No credit card required.
- Starter ($3.50/mo): Managed SMTP with automatic DKIM key generation and rotation. 14-day free trial (card required).
- Pro ($10/mo): Multiple sending domains, each with independent DKIM selectors. 14-day free trial.
- Agency ($23.25/mo): Manage DKIM across 100+ client domains from a single dashboard. Key rotation and monitoring at scale. 14-day free trial.
The point isn't convenience for its own sake. It's that a misconfigured DKIM record is invisible until your emails start bouncing. Automated validation catches the problem before your recipients notice.
Conclusion
To create DKIM record entries correctly, you need four things: a 2048-bit key pair, a DNS TXT entry under the right selector, an actively signing mail server, and a quick verification to confirm it all works. The whole process to create DKIM record entries takes ten minutes for a single domain.
Once you create DKIM record entries successfully, don't stop there. Pair it with SPF and DMARC to lock down your domain completely. Every week you operate without the full stack, you're leaving deliverability and brand security on the table.
If managing DNS records manually isn't your idea of a productive afternoon, try TrekMail free and let the wizard handle the configuration.