Catch All Mailbox Setup: 3 Safe Patterns That Protect Your Domain
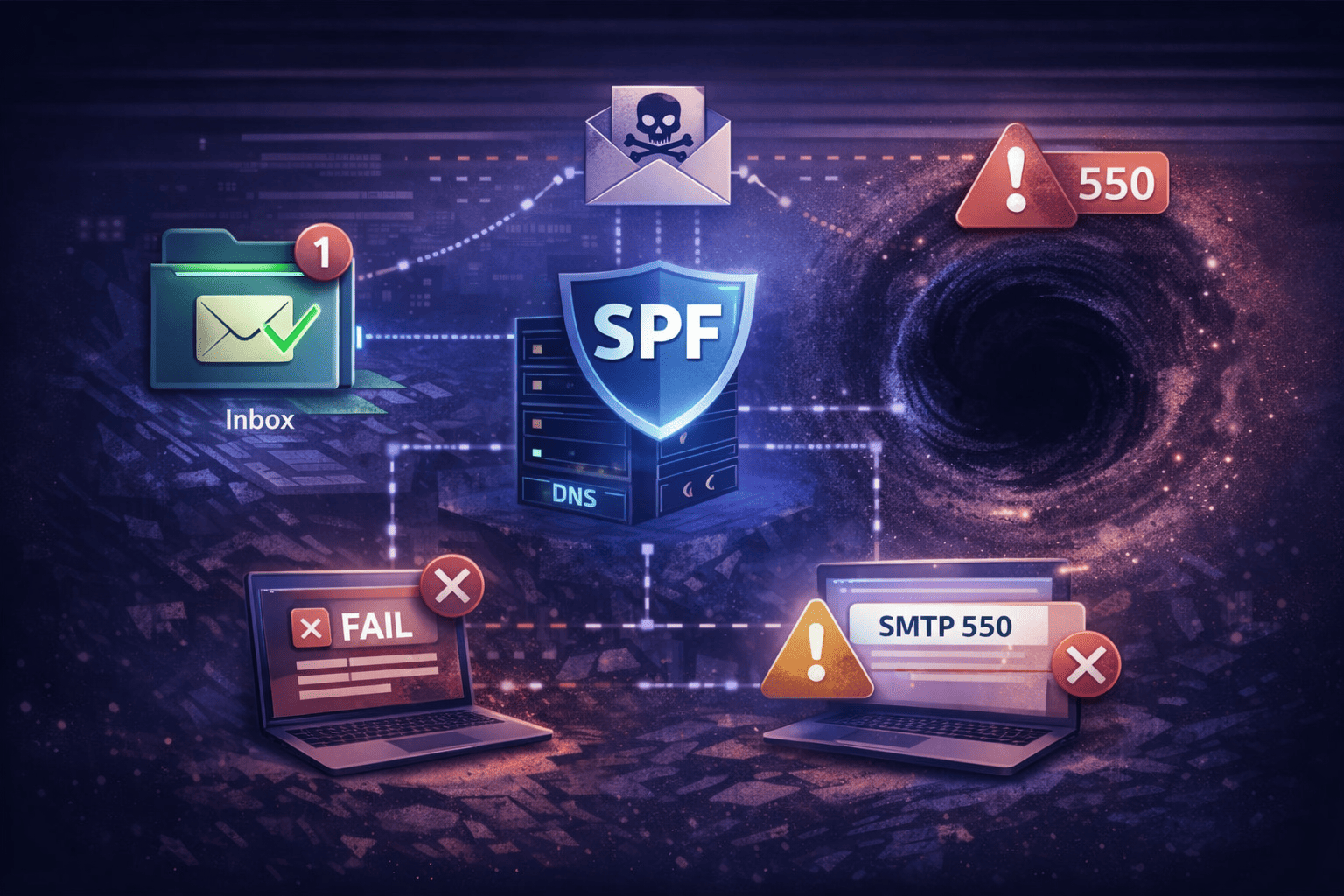
A catch all mailbox tells your mail server to accept every message sent to your domain—even when the recipient doesn't exist. Instead of bouncing typo@yourdomain.com with a 550 error, your server says "sure, I'll take it." That sounds useful until spam, phishing, and directory harvest attacks pour in through the open door.
I've seen domains lose their sender reputation within weeks of flipping on a catch-all without guardrails. The setup itself isn't complicated. Keeping it from becoming an ops disaster is the hard part.
This guide covers three isolation patterns that let you run a catch all mailbox safely—whether you're on Microsoft 365, a Linux stack, or Google Workspace. If you're still deciding whether you even need one, read our breakdown of domain catch-all email first.
What Is a Catch All Mailbox?
A catch all mailbox is a single inbox that receives every email sent to your domain that doesn't match an existing address. When someone emails misspelled-name@yourdomain.com, instead of bouncing, the message lands in this designated mailbox.
The problem: your server now accepts everything. Spam bots, phishing attempts, and automated directory scans all get a 250 OK response. Without isolation rules, that traffic mixes with your real mail and tanks your domain reputation.
The Golden Rule: Never Route to a Primary Inbox
This is non-negotiable. Catch-all traffic bypasses Directory-Based Edge Blocking (DBEB), meaning your server accepts the payload before validating the recipient. Routing that stream into ceo@company.com or any active inbox creates a security blind spot you won't notice until it's too late.
Every pattern below follows the same principle: isolate the catch-all stream from production mail.
Pattern 1: The Quarantine Sink (Microsoft 365 / Exchange)
This is the standard approach for orgs that need to keep catch-all mail for legal or discovery purposes but don't want it triggering notifications every five minutes.
How it works
- Ingest — Your server accepts mail for unknown recipients.
- Tag — A Transport Rule identifies the message as external and not addressed to a valid user.
- Suppress — The rule sets the Spam Confidence Level (SCL) to 9 (high confidence spam).
- Store — The message routes to a shared mailbox like
catchall-sink@yourdomain.com.
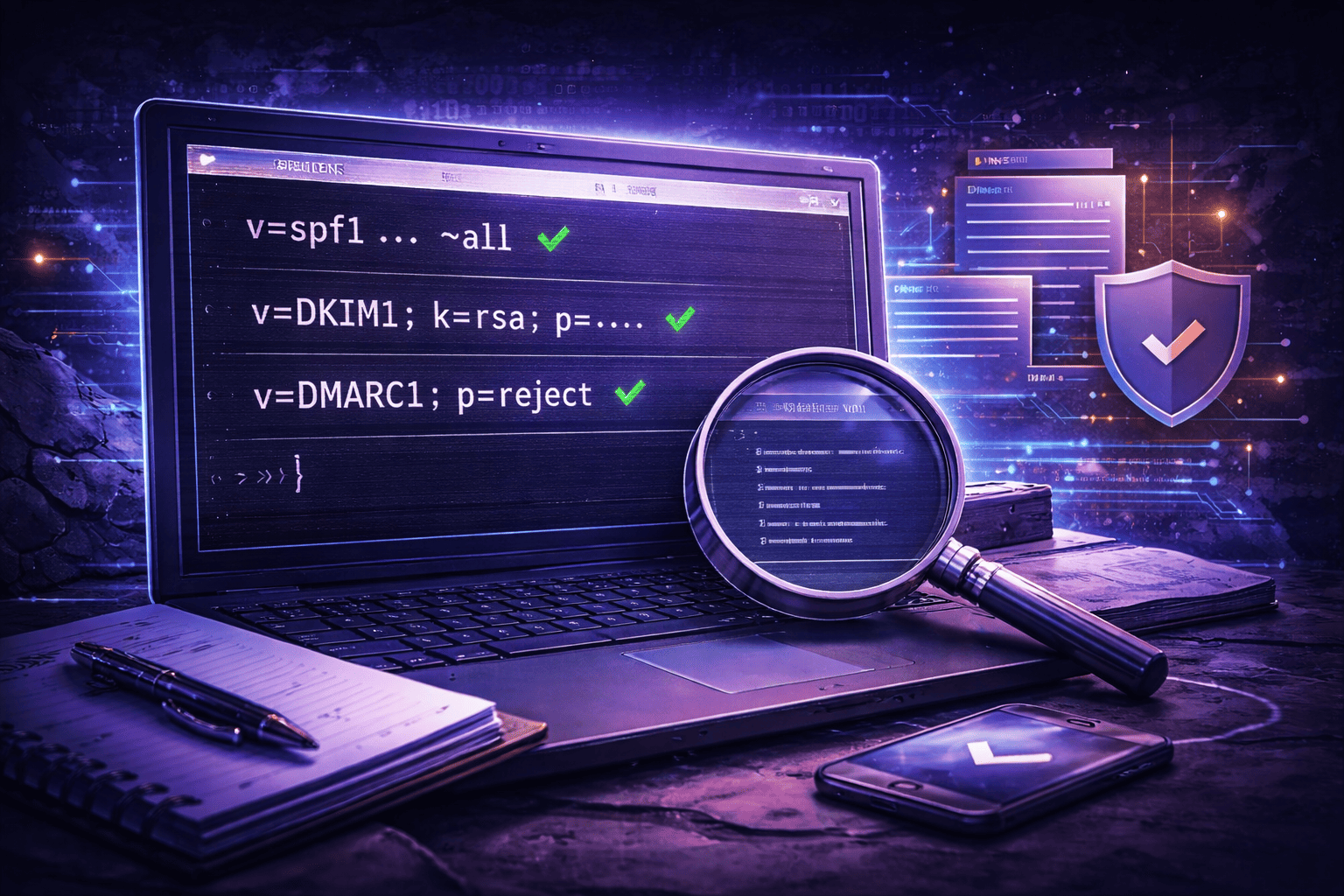
PowerShell setup
First, set your domain to "Internal Relay" in Exchange Admin Center (this disables DBEB). Then run:
# Create the sink (shared mailbox — no license needed)
New-Mailbox -Shared -Name "CatchAll Sink" -PrimarySmtpAddress catchall-sink@yourdomain.com
# Create the transport rule
New-TransportRule -Name "Catch-All Routing & Suppression"
-FromScope "NotInOrganization"
-SentTo "catchall-sink@yourdomain.com"
-RedirectMessageTo "catchall-sink@yourdomain.com"
-SetSCL 9
-ExceptIfRecipientBelongsTo "All Valid Users Group"Why SCL 9? Without it, the catch-all mailbox fills with notification noise. SCL 9 forces everything into the Junk folder. You review it weekly, not hourly.
Pattern 2: The Tagged Stream (Postfix / Linux)
If you're running your own Postfix/Dovecot stack, a separate mailbox might be overkill. Instead, inject a header and let client-side rules do the sorting.
How it works
- Ingest —
luser_relayaccepts the message for unknown local recipients. - Modify — The MTA injects an
X-Catch-All: Trueheader. - Filter — Sieve rules move the message to a dedicated folder.
Postfix configuration
# /etc/postfix/main.cf
# Route unknown local users to a specific alias
luser_relay = catchall_alias
# /etc/postfix/virtual
# Map the alias to a real user
catchall_alias realuser@yourdomain.comImportant: luser_relay only works for local domains. For multiple virtual domains, use virtual_alias_maps with a wildcard:
# /etc/postfix/virtual
@example.com realuser@example.comIf you're setting up email forwarding alongside catch-all rules, make sure your virtual maps don't conflict. Overlapping rules are one of the top causes of misrouted mail.
Sieve filter
Don't rely on your eyes to separate catch-all traffic. Automate it:
if header :contains "X-Original-To" "catchall_alias" {
fileinto "Junk/CatchAll";
stop;
}Pattern 3: The Partial Wildcard (Regex Routing)
This is the smartest approach when you don't actually need a true catch all mailbox. Instead of accepting *@domain.com, you accept only specific patterns—like sales-*@domain.com—and reject everything else.
How it works
You configure your MTA or email provider to accept addresses matching a regex (e.g., sales-webinar@, sales-q1@) while rejecting high-risk targets like admin@ or hr@.
Google Workspace setup
- Go to Apps > Google Workspace > Gmail > Default Routing.
- Under Specify Envelope Recipients, select "Pattern Match."
- Enter regex:
^sales-.*@yourdomain\.com$ - Set action: Change envelope recipient to
sales-team@yourdomain.com.
Result: sales-promo@yourdomain.com gets accepted. admin@yourdomain.com gets rejected with 550. This dramatically shrinks your attack surface for directory harvest attacks.
Need the addresses to actually function as email aliases? You can combine partial wildcards with alias forwarding for even more flexibility.
How to Prevent the Catch All Mailbox Routing Loop
The most dangerous failure in any catch all mailbox setup is the routing loop. Here's how it happens:
- Catch-all accepts mail for
ghost@domain.com. - A rule auto-forwards it to
external@gmail.com. - Gmail rejects it (SPF/DMARC failure).
- Gmail bounces the NDR back to
ghost@domain.com. - The catch-all accepts the bounce.
- The rule forwards the bounce to Gmail.
- Repeat until
MaxHopCountis exceeded.
You'll see errors like 5.4.14 Hop count exceeded or 5.4.6 Routing loop detected. On a busy domain, this can spike your outbound queue and trigger spam blocks within hours.
Prevention checklist
- Check headers — Make sure your MTA respects
X-LoopandDelivered-Toheaders. - Block auto-replies — Configure catch-all rules to skip messages with
Auto-Submitted: auto-generatedheaders. - Microsoft 365 gotcha — Outbound spam policy blocks external forwarding by default (error
5.7.520 Access denied). You must enable it in the Outbound Spam Filter Policy, but doing so increases backscatter risk. Weigh the tradeoff carefully.
For a deeper look at forwarding pitfalls across providers, see our guide on email alias forwarding.
Why Most Catch All Mailbox Setups Exist (and Shouldn't)
Let's be honest about the root cause. Most businesses turn on a catch-all to dodge per-seat licensing costs. If you need support@, billing@, and jobs@ but don't want to pay $18/month per seat to Google or Microsoft, the catch-all feels like a clever workaround.
It's not. It's technical debt with a reputation cost.
The real fix is a provider that doesn't charge per user. TrekMail uses pooled storage instead of per-seat pricing:
- Nano plan — $0, no card required.
- Starter — $3.50/mo with 14-day trial.
- Pro — $10/mo with 14-day trial.
- Agency — $23.25/mo with 14-day trial.
You create support@, billing@, and jobs@ as real mailboxes or aliases on your custom domain. They exist in the directory, so the server rejects invalid recipients at the edge with a proper 550 response. Your domain reputation stays intact. No Transport Rules, no Sieve filters, no regex routing.
If you're managing multiple domains—whether as an MSP or a growing business—stop fighting with catch-all workarounds. TrekMail's catch-all inbox feature gives you the safety net without the architectural risk.
Wrapping Up
A catch all mailbox isn't inherently bad. It's the unguarded catch-all that destroys domains. Pick the isolation pattern that fits your stack—quarantine sink for Exchange, tagged stream for Postfix, partial wildcard for Workspace—and enforce the golden rule: never mix catch-all traffic with production mail.
Or skip the complexity entirely. Use a provider that makes real addresses cheap enough that you don't need the catch-all in the first place.