Auto forward email rules feel like the easiest solution in email management — one redirect, job done. In practice, they're the leading cause of "I never received that" tickets, and in worse cases, the reason your domain ends up rate-limited by Gmail or flagged on an outbound spam blocklist with no obvious explanation.
The problem isn't configuration. It's the protocol. When you auto forward email, your server opens a new SMTP connection using its own IP address. That IP isn't in the original sender's SPF record. The receiving server sees something indistinguishable from a spoofed message. SPF fails. If the original sender runs a p=reject DMARC policy — which most banks, enterprise SaaS platforms, and government domains do — the destination drops the message silently. No bounce. No notification. No error. The email disappears.
This guide covers when auto forward email is technically safe, five structural patterns where it actively breaks mail flow or creates compliance and security risks, and the architectural alternatives that actually hold up. For the full protocol mechanics — SRS, ARC, bounce codes, and step-by-step setup — see the complete guide to email forwarding: how it works, how to set it up, and how to fix it when it breaks.
What Actually Happens When You Auto Forward Email
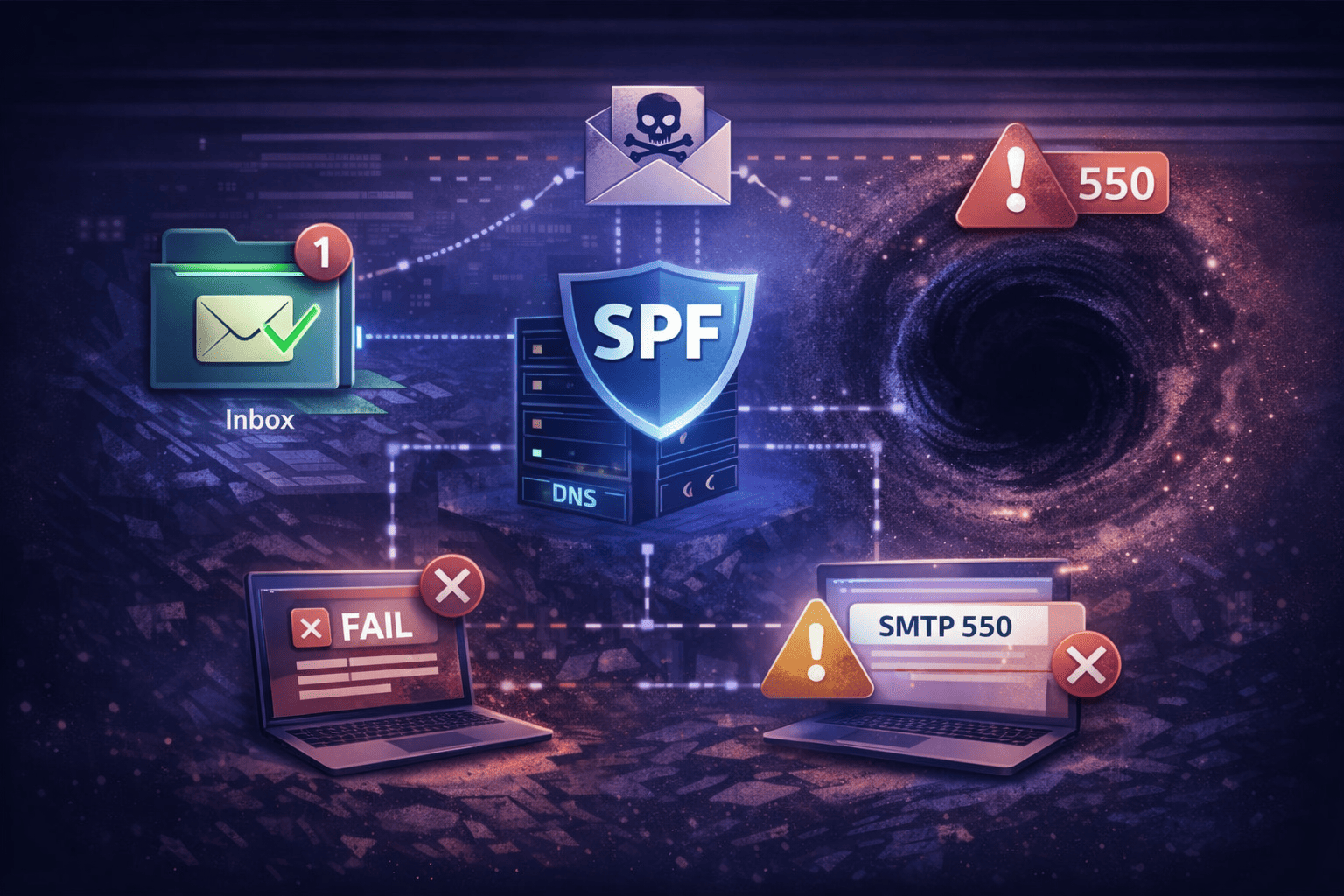
When you auto forward email, your server opens a new outbound SMTP connection from its own IP. That IP isn't authorized by the original sender's SPF record — SPF fails on the forwarded hop. If DKIM also breaks in transit, DMARC has nothing to verify. Under p=reject, the destination drops the message without notifying anyone. No bounce. No error on your end.
Three authentication layers interact on every forwarded message:
- SPF (Sender Policy Framework) — validates the sending IP against the envelope sender domain. Your forwarding server's IP isn't authorized by the original sender. SPF fails on every hop, every time, unless Sender Rewriting Scheme (SRS) rewrites the envelope sender to your domain first.
- DKIM (DomainKeys Identified Mail) — a cryptographic signature on message headers. Survives forwarding unless the message is modified in transit (an appended footer, a reformatted body). DKIM is your safety net when SPF fails.
- DMARC — requires SPF or DKIM to align with the From: header. Both fail? Under p=reject, the destination drops the message. The original sender gets no error. You get no error. It's gone.
ARC (Authenticated Received Chain), standardized in RFC 8617, is the modern protocol fix. Each forwarding hop adds a cryptographic seal recording the original authentication results. A receiving server that trusts the ARC chain can accept a message that would otherwise fail DMARC. The catch: both your MTA and the destination need ARC support — and most shared hosting MTAs don't implement it by default.
5 Traps That Make Auto Forward Email Dangerous
Auto forward email fails in five structural patterns. Some produce hard bounces with SMTP error codes you can track. Others fail silently — mail stops arriving, with no indication why. The silent failures are worse, because nobody knows until a customer mentions they never heard back from you.
1. The Compliance Trap (GDPR & HIPAA)
Scenario: Auto forward email from a business address to a personal Gmail or Yahoo account.
Under GDPR, you're processing personal data on a consumer platform where you're not the data controller and have no Data Processing Agreement. Under HIPAA, forwarding protected health information to a non-compliant server is an unauthorized disclosure. In litigation, you can't search, hold, or delete data sitting in personal inboxes outside your control perimeter.
There's no technical fix here. The problem is structural: regulated data has left your control perimeter, and it's not coming back.
2. The Spam Amplification Trap
Scenario: Auto forward email from a shared address — sales@, info@, support@ — to three employee mailboxes.
Every spam message that reaches the original address multiplies by three. Your server stamps your domain's return address on the envelope and relays it. The destination sees your domain as the sender of spam. Your IP reputation absorbs the hit for mail you didn't originate. Triple the inbound spam volume means triple the reputation damage, and it compounds over time.
There's also a state problem: if User A replies to a forwarded message, Users B and C have no visibility. No shared thread. No single source of truth.
3. The Rate-Limiting Trap
Scenario: Auto forward email — log alerts, server notifications, transactional mail — to a free Gmail account.
Consumer inboxes have strict receiving limits, roughly 60 messages per minute. If your server bursts alerts to a Gmail address, Google responds with a temporary 421 4.7.26 deferral. That block frequently extends to all mail from your domain to Gmail, not just the alerts. You've rate-limited your entire sending domain trying to route server logs to a personal inbox.
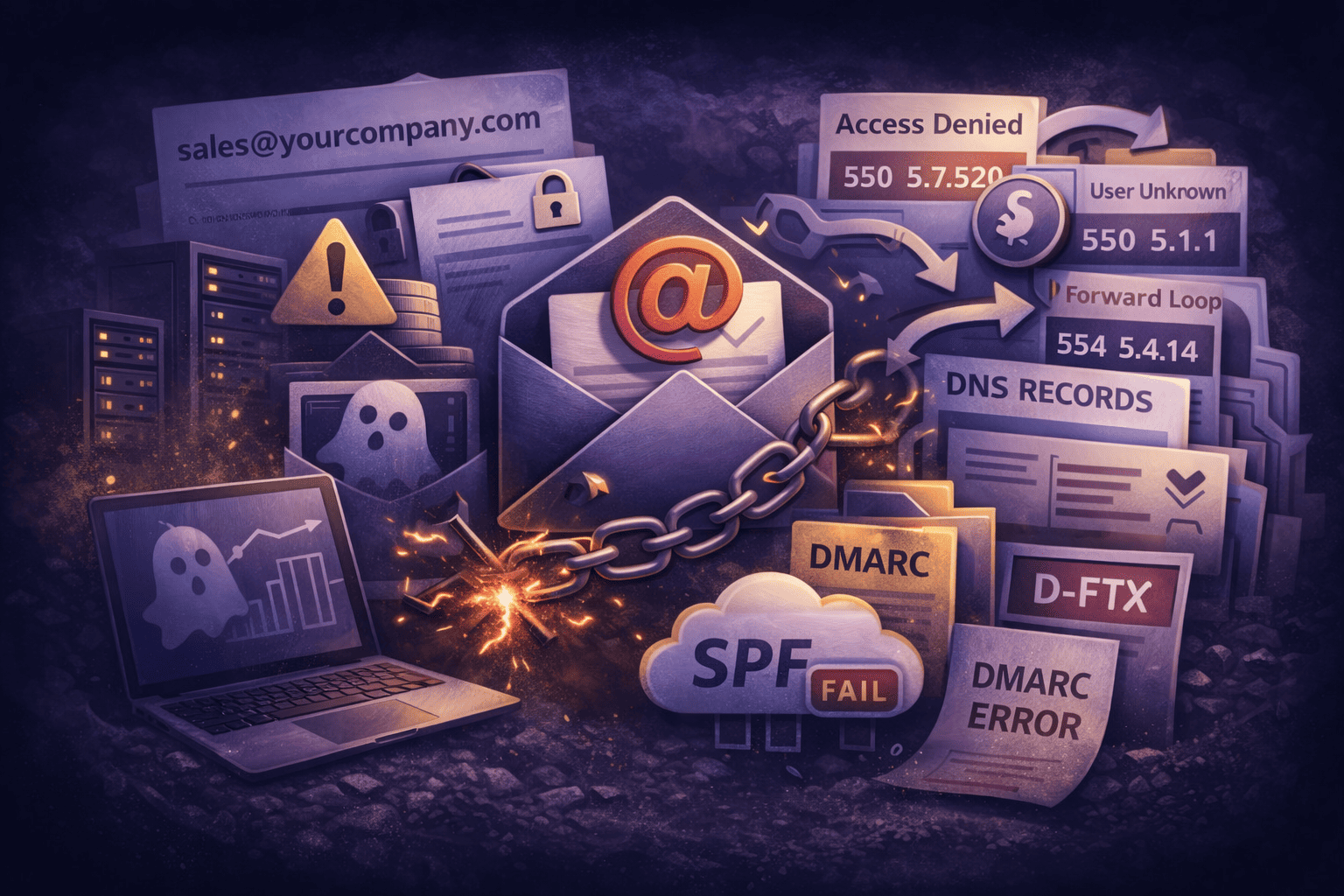
4. The BEC Attack Vector
Scenario: An attacker compromises a mailbox and creates a hidden auto forward email rule.
Business Email Compromise attackers routinely create rules to auto forward email containing keywords like "Invoice" or "Wire Transfer" to an external address, then move originals to Deleted Items. The rule runs silently. You appear to receive mail normally. The attacker gets copies of everything financially sensitive.
Microsoft 365 often blocks this pattern by default, generating NDR 550 5.7.520 Access denied — your organization does not allow external forwarding. That error is a feature, not a bug. If you're seeing it, an account may be compromised.
5. The Mail Loop (OOF Storms)
Scenario: User A has an active auto forward email rule to User B. User B has an Out-of-Office auto-reply running.
Here's what happens:
- An email arrives for User A.
- User A's server forwards it to User B.
- User B's server sends an auto-reply back to User A.
- User A's server forwards the auto-reply to User B.
- Repeat until the hop count limit is exceeded.
The result: NDR 554 5.4.14 Hop count exceeded — possible mail loop. Both users stop receiving mail until someone manually breaks the loop. Your MTA needs to respect X-Auto-Response-Suppress: All and Auto-Submitted headers to prevent this. If it doesn't, one OOF reply creates a meltdown.
When Auto Forward Email Is Actually Fine
Auto forward email is acceptable in three specific scenarios — not because the authentication risks disappear, but because the constraints are tight enough to prevent the failure modes from compounding. Each has a specific technical requirement or time limit that contains the risk.
Solo consolidation with SRS enabled
A single person consolidating me@startup.com into a personal inbox. This works if your forwarding MTA implements SRS to rewrite the envelope sender. Without SRS, you'll lose mail from any domain running a strict p=reject DMARC policy — banks, enterprise SaaS, government agencies. Verify SRS is active before trusting this setup with anything critical.
Short-term coverage (time-boxed)
Forwarding to a colleague during a leave of absence. The duration is short enough that even if authentication issues surface, they won't cause lasting domain reputation damage. Set an expiry date on the rule. Remove it when coverage ends — don't leave it running indefinitely.
Internal archival and compliance vaulting
Routing a copy of inbound mail to an internal compliance vault or archive@yourdomain.com. These systems are built to ingest raw mail streams and typically whitelist the source IP, bypassing standard spam filters. The destination is controlled infrastructure — not a consumer inbox with receiving limits and reputation scoring.
Safer Alternatives to Auto Forward Email
Safer alternatives to auto forward email replace fragile routing rules with patterns that don't create authentication gaps. For most use cases — team inboxes, identity management, temporary coverage — the alternative is simpler, more reliable, and eliminates authentication risk entirely.
| Goal | The Forwarding Approach (Risky) | The Better Approach (Safe) |
|---|---|---|
| Team access to a shared address | Auto forward sales@ to three mailboxes | Shared IMAP mailbox — one inbox, multiple users, one thread history. No data duplication. |
| Multiple addresses, one person | Auto forward ceo@ to john@ | Email alias — ceo@ is a label for john@. No network hop. Zero authentication risk. |
| Coverage during absence | Forward to an assistant's inbox | Delegated IMAP access — the assistant reads and replies directly from your mailbox. |
| Access on a personal device | Auto forward to a personal Gmail | Add the business account to Gmail as an IMAP account — no forwarding, no authentication risk. |
For a detailed breakdown of how aliases compare to forwarding across different scenarios, see domain email alias vs. mailbox — which one actually fits your setup.
Minimum Safe Checklist for Auto Forward Email Rules
If you must auto forward email and switching to an alias or shared mailbox isn't an option, run through these four checks before trusting the setup with real traffic. Skip any one of them and you're building on a foundation that will eventually fail silently.
1. Verify SRS is running
Send a test message to the forwarded address. At the destination, inspect the headers and check the Return-Path:
Pass:Return-Path: <SRS0=XXXX=TT=originaldomain.com=user@yourdomain.com>
Fail:Return-Path: <user@originaldomain.com>— SPF will fail for every p=reject sender
If you see the original sender's address in Return-Path, SRS is not active. Any mail from domains with strict DMARC enforcement will be silently dropped at the destination.
2. Set filter order: spam check before forward
Spam filtering must run before the auto forward email rule fires. If you relay unfiltered mail, you're laundering junk under your domain's reputation. Set the processing order explicitly: spam check first, then forward only clean messages. If your MTA doesn't support rule ordering, switch MTAs.
3. Confirm loop prevention headers
Your MTA must respect X-Auto-Response-Suppress: All and Auto-Submitted headers. Without this, a single active OOF auto-reply in the forwarding chain creates a mail loop. Test it in a controlled environment before it happens in production with a customer on the other end.
4. Monitor DMARC reports
Enable aggregate DMARC reporting on your domain. If forwarded auto forward email traffic starts failing — especially from p=reject senders — you'll see it in the reports before users start asking why their mail isn't arriving. At that point: implement ARC sealing on your MTA or migrate affected users to IMAP fetch instead of forwarding.
For the full DNS configuration covering SPF, DKIM, DMARC, and ARC, see secure email for business: the configuration baseline.
How TrekMail Handles Auto Forward Email
TrekMail manages the parts that break most auto forward email setups: SRS rewriting and ARC sealing run server-side automatically. You define the forwarding route in the dashboard; the header management happens behind the scenes. Forwarded mail leaves with a properly rewritten envelope sender, so SPF doesn't fail at the destination.
For teams that need shared access to a single address, TrekMail supports shared mailboxes accessible via IMAP from any client — one inbox, multiple users, one thread history. No forwarding rules. No state desynchronization. No spam amplification.
For agencies managing forwarding rules across dozens or hundreds of domains: TrekMail's multi-domain dashboard lets you apply routing templates at scale. Set a rule once, push it to 100 domains. No per-domain configuration work. No per-user fees for forwarding routes. Plans start at $3.50/month on Starter — see TrekMail pricing for the full breakdown.
The Nano plan is always free — no credit card, no expiry, 10 domains included. If you need managed SMTP with SRS handling and the full dashboard, the 14-day free trial covers all paid plan features (credit card required to start).
Auto forward email is a useful tool when it's configured correctly. When it's not, it's the reason your most important emails are disappearing without a trace. Set it up right, or replace it with something that doesn't require it. Try TrekMail.