A catch all email is a mail server setting that accepts messages sent to any address at your domain—even if no matching mailbox exists. Type ghost@yourdomain.com and hit send: a normal server rejects it with a 550 error and closes the connection before transferring a single byte. A catch all email setup says 250 OK, accepts the full payload, and drops it in a bucket mailbox.
That's the appeal. In 2026, it's also how you flood your server with garbage, destroy your domain reputation, and create GDPR exposure your legal team won't enjoy.
This guide covers exactly how the mechanism works at the SMTP level, the five ways it damages production infrastructure, what it does to your authentication stack, and what to configure instead.
What Is a Catch All Email?
A catch all email (also called an accept-all or wildcard policy) is a configuration that tells your mail server to accept messages for any recipient at your domain, regardless of whether a matching mailbox exists. Rather than rejecting unknown addresses with a 550 error at the connection stage, the server accepts the full message and routes it to a designated bucket mailbox. Your domain stops enforcing valid addresses and starts accepting everything the internet sends its way.
The terms "accept-all" and "catch-all" are used interchangeably across hosting control panels. Both describe the same behavior: the RCPT TO directory check is bypassed, and all inbound mail for unknown recipients flows into one designated mailbox. On TrekMail, you configure this per-domain under Domains → Connection → Catch-all Inbox—pick a target mailbox, and the setting applies immediately.
That was a defensible tradeoff in the late 1990s when spam was rare and most senders were humans who occasionally mistyped an address. The internet in 2026 is not that environment. Automated spam sources, directory harvest tools, and botnet mailers probe your domain around the clock. A catch-all means they never hit a wall.
Why Operators Enable Catch All Email (and Why They Regret It)
Two forces drive most catch all email decisions: fear of missing a lead, and the pain of per-seat pricing. Both are real problems. The catch-all is the wrong solution to both—it trades a hypothetical risk (missing a typo'd email) for a guaranteed one (spam floods and reputation damage).
The Fear-of-Missing-Out Driver
Small business owners worry that a prospect will type suport@ instead of support@ and never hear back. They treat the catch-all as insurance against sender typos. The problem: your bucket will receive thousands of spam messages for every one legitimately misaddressed email. That needle isn't worth the haystack—and the noise makes the needle impossible to find anyway.
The actual fix for typo anxiety is a short list of explicit aliases covering common misspellings. If your main address is support@, you can also create suport@ and route both to the same mailbox. Surgical, zero spam exposure.
The Per-Seat Tax Driver
Google Workspace and Microsoft 365 charge $6–30 per user per month. If your business needs support@, billing@, jobs@, and marketing@, that's four seats—up to $120/month—before anyone does actual work. The shortcut: create one real mailbox, enable a catch all email policy, receive everything for the price of one seat.
The trade-off is your domain reputation, your spam filter's sanity, and your legal team's patience. This is a pricing problem, not a technical one. Flat-rate providers exist specifically because per-seat pricing creates exactly this perverse incentive. You shouldn't have to compromise deliverability to save money on address management. See TrekMail's flat-rate plans for a direct comparison.
How It Works at the SMTP Level
Understanding catch all email starts at the SMTP level. The critical moment in any SMTP transaction is the RCPT TO command—when the sending server specifies the intended recipient before any message data is transferred. How your server responds to this single command determines whether you've built a secure mail system or an open intake valve. Everything else follows from this choice.
The Secure (Standard) Flow
S: EHLO mail.sender.com
S: MAIL FROM: <sender@sender.com>
S: RCPT TO: <ghost@yourdomain.com>
R: 550 5.1.1 User unknown
(connection closed — zero bytes of message body transferred)
Your server checks its user directory. No mailbox named ghost exists. It responds with 550 and drops the connection before a single byte of message body is transmitted. The sender gets a clear signal. No storage consumed. No CPU spent scanning. No data accepted.
The Catch-All Flow
S: EHLO mail.sender.com
S: MAIL FROM: <sender@sender.com>
S: RCPT TO: <ghost@yourdomain.com>
R: 250 OK
(full message body, headers, attachments transferred)
→ routed to catchall-bucket@yourdomain.com
Your server skips the directory check entirely. It accepts the full message—body, headers, attachments, and any payload—then routes it to the bucket. You've now stored data you never requested, from a sender you didn't authorize, to an address that doesn't exist.
This distinction matters enormously at scale. Edge rejection is cheap—the connection closes before any data moves. Accepting means scanning, storing, indexing, and processing every message before your spam filter can discard it. When a botnet runs a directory harvest against your domain, the difference between edge rejection and catch-all acceptance is the difference between a no-op and a server under load.
The 5 Real Risks in Production
When you enable a catch-all on a production domain, you're telling the internet you'll accept anything sent to it. Spammers, harvesters, and botnet operators take you up on that offer within hours of DNS propagation. Here's what happens to your infrastructure in the first few months.
Risk 1: The Noise Flood (Directory Harvest Attacks)
Catch all email makes your domain a soft target for Directory Harvest Attacks (DHA), which map valid addresses at your domain. They blast millions of common prefixes—admin, david, invoice, hr, webmaster, noreply—at your server, checking which ones bounce and which ones don't.
Without a catch-all: your server rejects every invalid guess at the connection stage with a 550 error. The attacker's script hits a wall and moves to a softer target. With a catch-all active: your server accepts every guess. A domain that normally processes 50 emails a day can suddenly be ingesting 50,000—burning storage quotas, consuming filter resources, and burying real client email under an avalanche of junk.
Risk 2: Backscatter and Sending Reputation Damage
Backscatter is the silent killer of catch all email setups, and it works as follows:
- A spammer sends a message to
random-gibberish@yourdomain.com, which has a catch-all enabled. - They forge the
Return-Pathheader to point at an innocent victim:victim@gmail.com. - Your catch-all accepts the message.
- Your spam filter scans it, determines it's junk, and rejects it after the fact.
- Your server generates a Non-Delivery Report (NDR) and sends it to the
Return-Path:victim@gmail.com. - You just sent unsolicited email to an innocent person on behalf of a spammer.
To Gmail, your server is harassing their users with unwanted bounce messages. Do this at scale and your sending IP ends up on blocklists like ips.backscatterer.org. Your legitimate business email starts landing in Junk folders. The connection between an inbound configuration mistake and outbound deliverability failure isn't obvious until it bites you. Our article on why email domain reputation tanks covers the full picture and the recovery process.
Risk 3: Routing Ambiguity
Catch all email creates routing ambiguity. An email arrives for partnerships@company.com. It lands in the catch-all bucket. Who checks it? The CEO? Sales? The office manager? The answer is usually "everyone and no one." Critical messages sit unread for days because each person assumes someone else handled it. By the time the email surfaces, the deal is cold and the sender has moved on.
Explicit aliases solve this immediately. You define who owns each address at creation time. There's no ambiguity about where partnerships@ goes because you configured the routing explicitly.
Risk 4: The MSP Support Burden
For agencies managing 50+ client domains, catch-alls are a predictable ticket generator:
- "My mailbox is full and loading slowly." (Catch-all bucket hit its storage limit with spam.)
- "I'm getting too much junk mail." (Catch-all traffic bypassing or overwhelming edge filters.)
- "I can't find the email from my client." (It's on page 400 of the catch-all inbox.)
- "My outbound emails are going to spam." (Backscatter damaged the sending IP's reputation.)
Disabling catch-alls and migrating clients to explicit aliases reduces mailbox-related support tickets dramatically—typically 30–40% fewer in the first month. The time you save on triage pays for the alias setup many times over.
Risk 5: Compliance and GDPR Liability
A catch all email setup conflicts with GDPR Article 5(1)(c), which requires data minimization: collect only what you need for a specified, legitimate purpose. A catch-all collects everything, including unsolicited personally identifiable information from random strangers who mistype an address or from spammers using your domain as a dump.
When a user invokes the right to erasure, finding their data inside a bucket containing 500,000 spam messages is a needle-in-a-haystack exercise your legal team will bill by the hour. In healthcare environments, if a patient emails doctor@yourclinic.com and it lands in a catch-all accessible by IT staff without clinical authorization, you have a potential HIPAA unauthorized disclosure. The regulatory exposure is disproportionate to any benefit the catch-all provides.
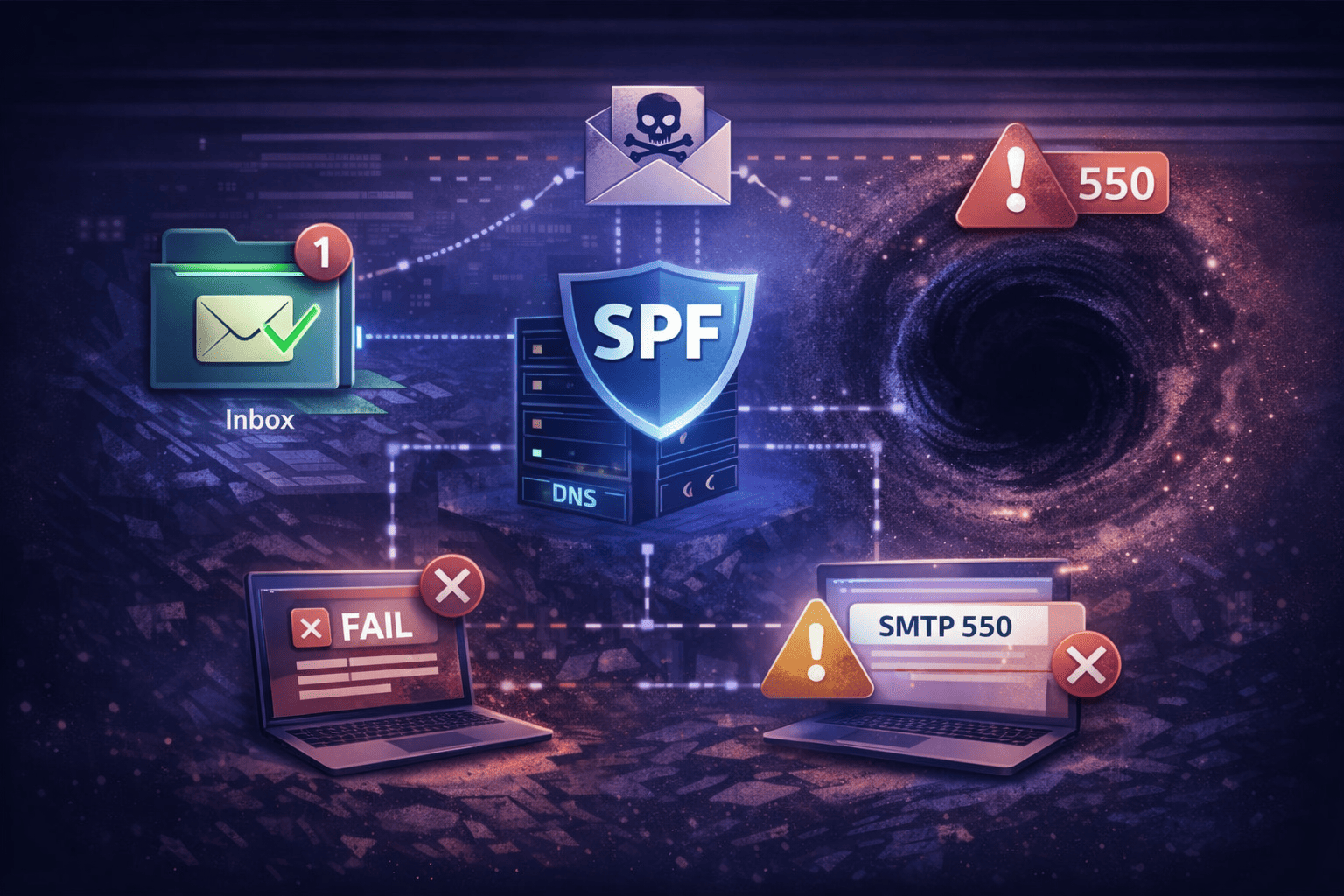
How Catch All Email Breaks SPF, DKIM, and DMARC
A catch all email configuration doesn't break authentication protocols directly—but it creates the conditions that cause them to fail. The spam traffic it attracts generates authentication anomalies, backscatter events, and forwarding chain failures that degrade your domain's standing with receiving servers over weeks and months. The damage is indirect and cumulative, which makes it hard to diagnose.
| Protocol | What It Checks | Catch-All Impact |
|---|---|---|
| SPF | Whether the sending IP is authorized by the domain's DNS TXT record | Doesn't break SPF directly, but backscatter bounce traffic amplifies SPF-fail complaint patterns attributed to your domain |
| DKIM | Cryptographic signature on message headers and body content | Forwarders processing catch-all traffic often modify messages (footers, subject rewrites), breaking existing DKIM signatures |
| DMARC | Alignment between SPF/DKIM results and the visible From: domain | Forwarded catch-all mail almost always fails DMARC at the next hop—the envelope and header From domains no longer match |
The real damage concentrates at forwarding. When catch-all traffic gets forwarded downstream, your domain stops being a passive spam receiver and becomes an active relay. Every forwarded message carries your domain's name and your sending IP's reputation. When DMARC checks fail at the receiving end, the failure is attributed to your domain in aggregate reporting. You can track how receiving servers see your domain's authentication signals using Google Postmaster Tools—checking this regularly is the earliest warning system for reputation degradation.
The Forwarding Problem
The most dangerous catch all email pattern isn't a production mail server with careful routing—it's someone who bought a domain, enabled a catch-all, and forwarded everything to their personal Gmail. The expectation: manage business mail from a familiar inbox. The reality: you lose mail regularly and you won't know why until a client asks why you never responded.
Why Forwarded Mail Fails Authentication
When you forward a message, you're re-sending it from your server to the final destination. The receiving server sees the message arriving from your IP—but the visible From: header still says the original sender (e.g., bank@chase.com). Authentication checks run against that mismatch:
- SPF check: Gmail checks Chase's SPF record. Your forwarding server's IP isn't listed. SPF fails.
- DKIM check: If your forwarding server modified the message in any way—added a footer, rewrote the subject line, stripped an attachment—the DKIM signature is broken.
- DMARC check: With SPF failing and DKIM potentially broken, DMARC has no passing signal to align on. Depending on the sender's DMARC policy, the message is quarantined or silently dropped.
Silently dropped means no bounce, no error, no notification. The message disappears and you never know it existed. For banks, insurers, and major SaaS platforms that enforce strict DMARC policies (p=reject), this happens constantly with naive forwarding setups. Our guide on email forwarding troubleshooting and setup covers diagnosis and remediation in detail.
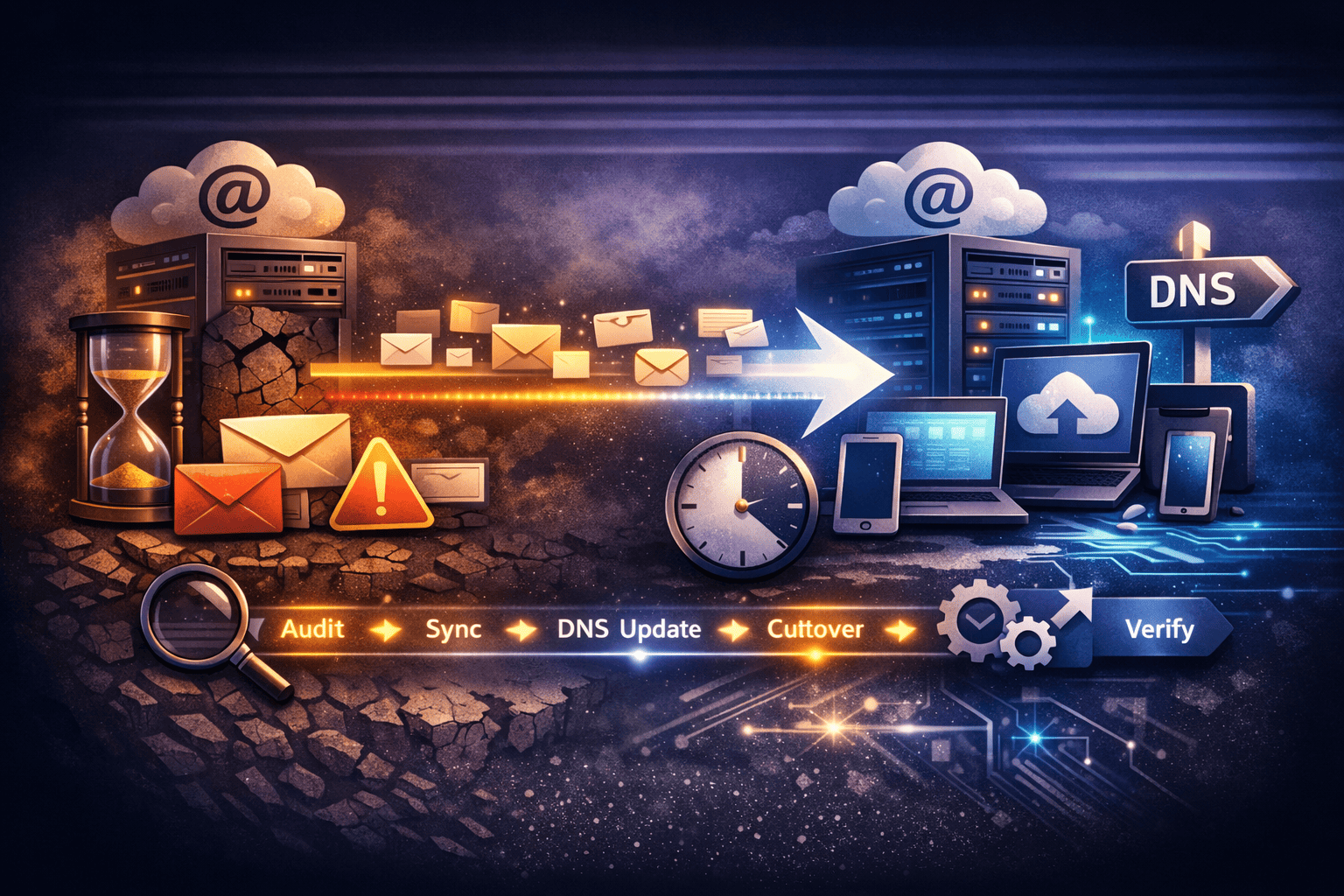
When You Have to Forward Anyway: SRS and ARC
If you're forced to forward catch all email traffic to an external mailbox—during a migration, for a legacy workflow, or as a temporary bridge between systems—standard forwarding will break authentication. Two technologies exist to address this: SRS handles the envelope rewriting problem, and ARC handles the authentication vouching problem. You typically need both.
SRS (Sender Rewriting Scheme)
SRS rewrites the envelope sender address during forwarding so SPF checks at the receiving end pass against your domain's SPF record rather than the original sender's.
Before SRS
Envelope From:alice@example.comAfter SRS
Envelope From:SRS0=HASH=TT=example.com=alice@your-forwarder.comThe receiving server checks SPF for
your-forwarder.com. You control that domain and its authorized sending IPs. SPF passes.
SRS fixes the SPF problem but doesn't fix DMARC alignment. The visible From: header still reads alice@example.com. The envelope now reads your-forwarder.com. They don't share a root domain. DMARC requires alignment, so DMARC still fails unless the original DKIM signature remains intact and valid. If your forwarder modified the message at all, that signature is gone. For the full technical walkthrough, see our guide on SRS email forwarding.
ARC (Authenticated Received Chain)
ARC is the protocol designed to solve the forwarding authentication problem that SRS alone can't fix. When your server forwards a message, ARC lets it add a set of cryptographically signed headers asserting: "I received this message, I verified its authentication at that point, and I'm vouching for those results now."
Receiving servers that trust your ARC signature—primarily Gmail and Microsoft—honor the original authentication results even if SPF has since failed. ARC is defined in RFC 8617 and is increasingly required for reliable forwarding chains involving high-security senders.
The critical caveat: ARC only works if your forwarding server has a good sending reputation and is recognized as a legitimate intermediary. A catch-all inbox that's been processing thousands of spam messages per day is unlikely to be on anyone's trusted forwarder list. The backscatter reputation problem and the ARC trust problem compound each other—you need to fix the catch-all before ARC vouching becomes useful.
Configuring Catch All Email Safely (If You Must)
If your business genuinely requires catch all email—legacy system compatibility, a migration safety net, typo recovery for a high-value domain—you must implement guardrails. Routing catch-all traffic directly to an active human inbox is not acceptable in production. Here are three strategies that contain the damage.
Strategy A: The Quarantine Sink
Treat catch all email as radioactive. Never deliver it to a real inbox directly.
- Create a dedicated mailbox:
catchall-quarantine@yourdomain.com. Do not grant it "Send As" rights. It is receive-only. - Configure your mail server or transport rule to route all unknown recipients to this mailbox.
- On Microsoft 365: set the SCL (Spam Confidence Level) to 9 for all traffic hitting this rule. This forces it into Quarantine or Junk and suppresses mobile push notifications.
- Review schedule: check it once per week, or only when a client reports sending to the wrong address. Do not monitor it live.
On TrekMail, you can point the catch-all to a dedicated mailbox with filtered views—keeping it fully isolated from your primary mailboxes while still being searchable if you need to recover a specific misdirected message.
Strategy B: Microsoft 365 — DBEB vs. Internal Relay
Exchange Online runs in Authoritative Mode by default, which enables DBEB (Directory-Based Edge Blocking): Microsoft's servers reject invalid recipients at the network edge before accepting message data. This is secure and resource-efficient.
To enable a catch-all on Exchange Online, you typically switch the domain to Internal Relay Mode. This disables DBEB. Microsoft's servers must now accept every inbound message for your domain before your transport rules can inspect it. During a Directory Harvest Attack, this means Microsoft ingests and processes tens of thousands of spam messages per hour on your behalf—which can throttle delivery for legitimate recipients in your tenant.
Strategy C: Partial Wildcards (Postfix)
Advanced Postfix configurations support prefix wildcards on virtual alias maps, giving you catch-all behavior for specific patterns only:
# /etc/postfix/virtual
sales-*@yourdomain.com sales-bucket@yourdomain.com
This accepts sales-q1@, sales-webinar@, sales-2026@—disposable tracking addresses for marketing campaigns—while still rejecting admin@, hr@, and other prefixes that harvesters probe aggressively. You get the flexibility without opening the entire domain.
| Strategy | Spam Exposure | Admin Overhead | Best For |
|---|---|---|---|
| Full catch-all → active inbox | Very high | High (daily triage) | Nobody in production |
| Quarantine sink | Contained | Low (weekly check) | Typo recovery, migration safety nets |
| Internal Relay + SCL=9 (M365) | Medium | Medium | Exchange Online legacy setups |
| Partial wildcards (Postfix) | Low | Medium (pattern maintenance) | Marketing tracking, disposable addresses |
| No catch-all + explicit aliases | None | Very low | Everyone else |
The Better Alternative: Aliases and Explicit Routing
The right answer for almost every business that thinks it needs a catch all email setup is actually a set of explicit aliases with defined routing rules. Aliases give you full flexibility to receive mail at many addresses without any of the catch-all's operational baggage—no spam floods, no authentication failures, no ambiguous ownership, no GDPR exposure from unsolicited data.
Aliases vs. Mailboxes vs. Catch-All: Decision Table
| Explicit Alias | Full Mailbox | Catch-All Bucket | |
|---|---|---|---|
| Creates storage | No (forwards to mailbox) | Yes | Yes |
| Spam exposure | Targeted (known address only) | Targeted | Everything the internet sends |
| Authentication risk | Low (SRS-aware forwarding) | None | High when forwarded downstream |
| Per-seat cost | Free on flat-rate plans | $6–30/mo on per-seat plans | Appears free; hidden cost in spam overhead |
| GDPR exposure | Minimal | Controlled | High (unsolicited PII collection) |
| Ownership clarity | Explicit (defined routing) | Explicit | None (bucket ownership is ambiguous) |
The catch-all "appears free" row is deceptive. The cost materializes as spam filter licenses, storage overages, IT support hours, and eventually a damaged domain reputation that takes months to rehabilitate. For a full breakdown of the alias vs. mailbox decision—including when each is the right choice—read our guide on email aliases: definition, setup, and when to use them.
What to Create Instead
Map the addresses your business actually uses. Most companies need five or fewer:
hello@orinfo@— general inquiries, routes to founder or ops inboxsupport@— customer support, routes to helpdesk or shared inboxbilling@— invoicing and payments, routes to financejobs@orcareers@— recruiting, routes to HR or an ATS webhooknoreply@— transactional sending, receives nothing or discards silently
Five explicit aliases replace catch all email entirely. Zero spam flood. If a prospect types helo@ instead of hello@, they get a clear 550 bounce and try again. That outcome is better than their message sitting unread in a spam-saturated bucket for three weeks.
TrekMail's Approach to Catch All Email
TrekMail supports catch all email on every plan—but the way TrekMail is priced makes it far less necessary than on per-seat providers. The entire reason operators reach for the catch-all is usually financial. Remove that pressure and most of the use cases disappear.
The Old Way (Per-Seat Providers)
Pay $6–30/month per mailbox. Need support@, billing@, jobs@? Three extra seats, up to $90/month more before your team does any work. Financial pressure pushes you toward enabling a catch-all to avoid the bill. You inherit every problem documented in this article in exchange for saving a few dollars per month.
The TrekMail Way
Flat-rate pricing eliminates the financial reason for catch all email workarounds. Pooled storage across all your domains. Create as many mailboxes and aliases as your business needs—no per-address charge. The Starter plan at $3.50/month covers 50 domains. The Pro plan at $10/month covers 100. There's no financial incentive to use a catch-all as a cost-saving workaround because the incremental cost of another alias is zero.
For teams that genuinely need a catch-all—migration safety nets, legacy system compatibility, typo recovery on a high-volume domain—TrekMail provides a dedicated catch-all inbox per domain with proper quarantine-aware routing. You route catch-all traffic to an isolated mailbox without affecting your primary mailboxes. Full setup details are in the TrekMail catch-all inbox documentation.
Ready to retire the catch-all workaround? Start a 14-day free trial—no per-seat fees, no reason to cut corners on routing.
Frequently Asked Questions
These are the questions operators ask most often about catch-all configuration—whether they're evaluating it for the first time or trying to disable one that's caused problems.
What is catch all email?
A catch all email is a mail server setting that accepts messages addressed to any recipient at your domain, including addresses that don't exist as real mailboxes. Rather than rejecting unknown addresses with a 550 error, the server routes all unmatched traffic to a single bucket mailbox. It's called "accept-all" in some interfaces and "wildcard routing" in others—same behavior, different labels.
Is catch all email safe to use?
Not for most production environments. Enabling catch all email exposes your domain to directory harvest attacks, backscatter reputation damage, DMARC failures on forwarded mail, and GDPR data minimization violations. If a specific workflow genuinely requires it, isolate the traffic in a quarantine sink, apply maximum spam scoring, and review it no more than weekly. Never route it to an active primary inbox.
Does catch all email affect outbound deliverability?
Yes, significantly. The spam volume a catch-all attracts leads to backscatter bounce events that register against your sending IP. If you forward catch-all traffic downstream, the resulting authentication failures (SPF, DKIM, DMARC) register against your domain in aggregate reports. Your outbound deliverability degrades because of an inbound configuration choice. The connection isn't obvious until your legitimate business emails start landing in Junk folders.
What's the difference between a catch-all and an email alias?
An email alias routes mail from one specific, explicitly defined address to another mailbox. You decide which addresses exist and where they go. A catch-all routes mail from any address—including ones that don't exist—to a bucket mailbox. Aliases are surgical and intentional. The catch-all is a wide-open door. For most businesses, a set of five explicit aliases replaces every legitimate use case the catch-all was serving.
Can I use a catch all on Google Workspace or Microsoft 365?
Yes, both support it. On Google Workspace, you configure a Default Routing rule in the Admin Console to forward unmatched recipients to a designated account. On Microsoft 365, you typically switch the domain to Internal Relay Mode, which disables Directory-Based Edge Blocking (DBEB)—meaning Microsoft's servers must accept every inbound message for your domain before transport rules can act. During a spam attack, this creates processing delays for legitimate mail in your tenant. On both platforms, per-seat pricing is what makes catch-alls attractive as a workaround, which is why the problems in this article are so common among their customers.
How do I disable a catch all email configuration?
Disabling catch all email depends on your mail platform. On cPanel/WHM: Email Routing → Default Address → set to "Fail with error" or "Discard." On Google Workspace: Apps → Google Workspace → Gmail → Default routing → remove the catch-all rule. On Microsoft 365: Exchange Admin Center → switch domain back to Authoritative mode to re-enable DBEB. On TrekMail: Domains → [domain] → Connection tab → Catch-all Inbox → set to "No catch-all." Allow 24–48 hours for mail flow to stabilize after any routing change.
What should I use instead of a catch all?
Explicit aliases with defined routing. Map the addresses your business actually uses—usually five or fewer—to specific mailboxes or shared inboxes. If per-seat pricing is driving the decision, switch to a flat-rate email provider. There's no reason to compromise domain reputation and authentication reliability to avoid paying per address. The cost of cleaning up a damaged sending reputation is always higher than the seat cost you were trying to avoid.